Hello there!
Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
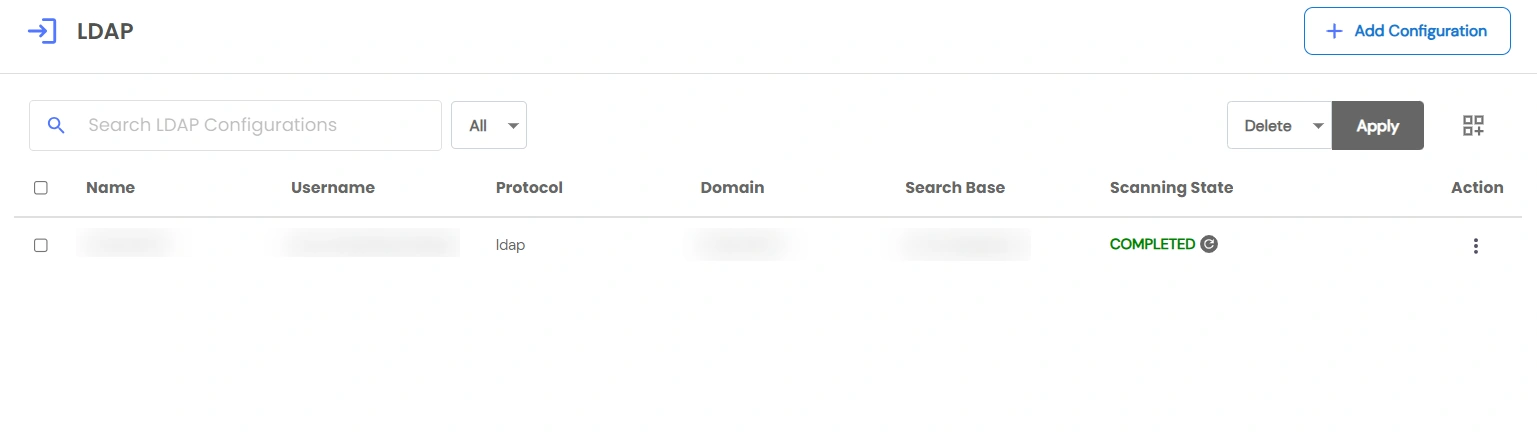
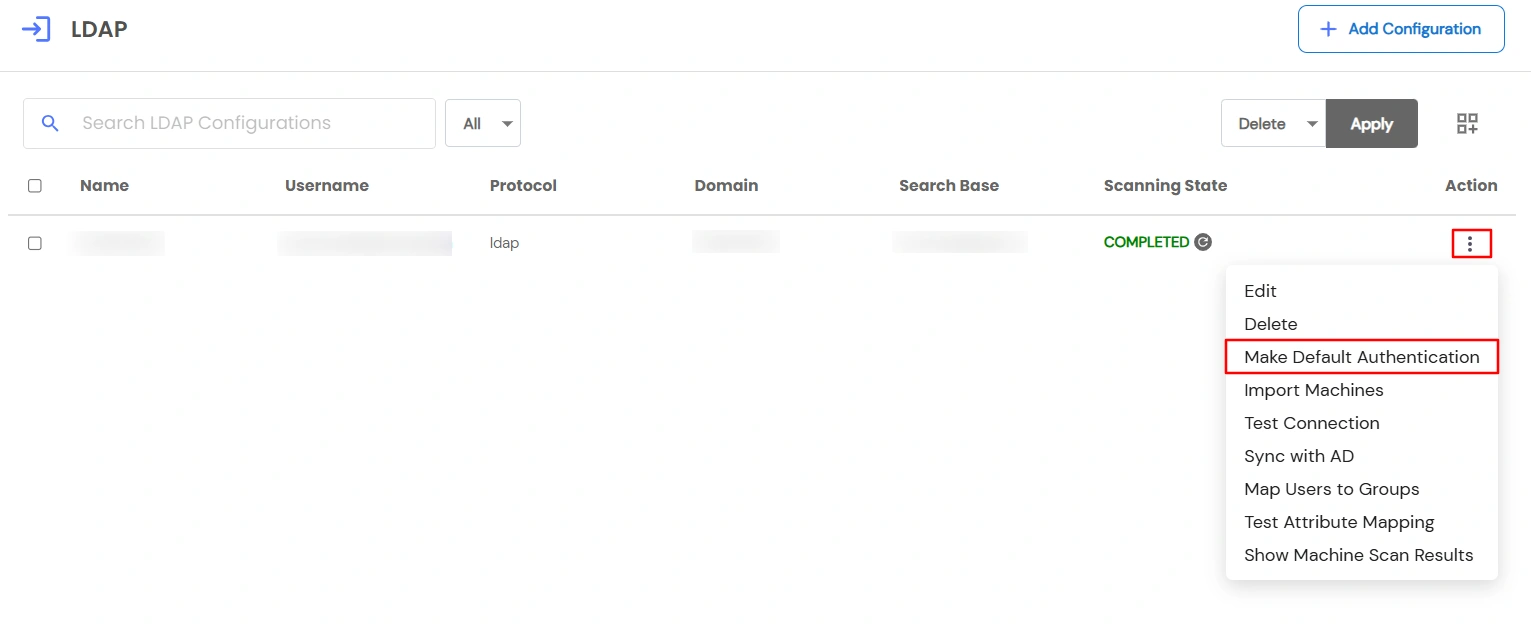
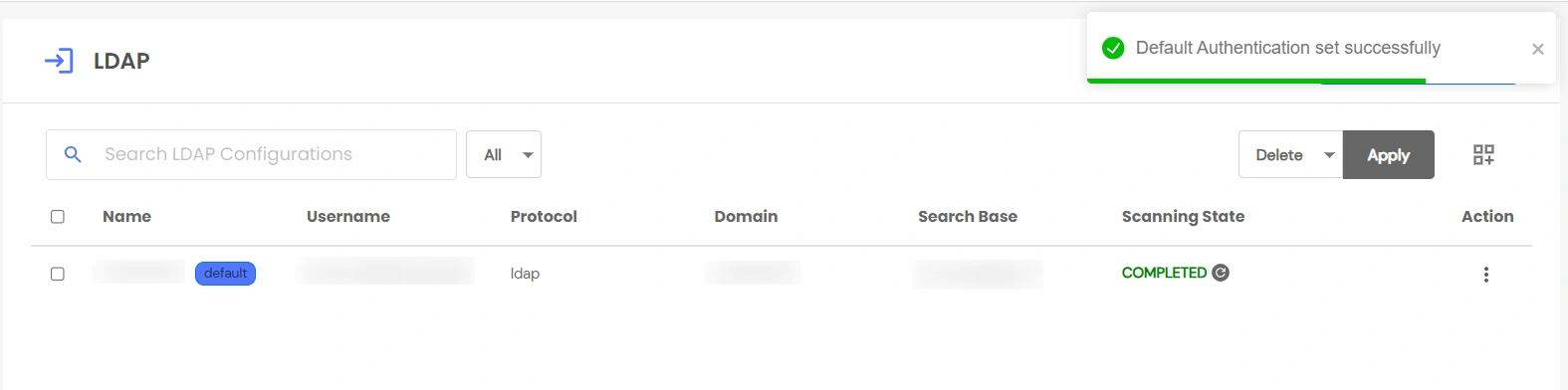
×This feature allows users to authenticate into PAM using their Active Directory (AD) credentials via the LDAP/LDAPS protocol.
The authentication flow first checks if an AD configuration is set as the default authentication.
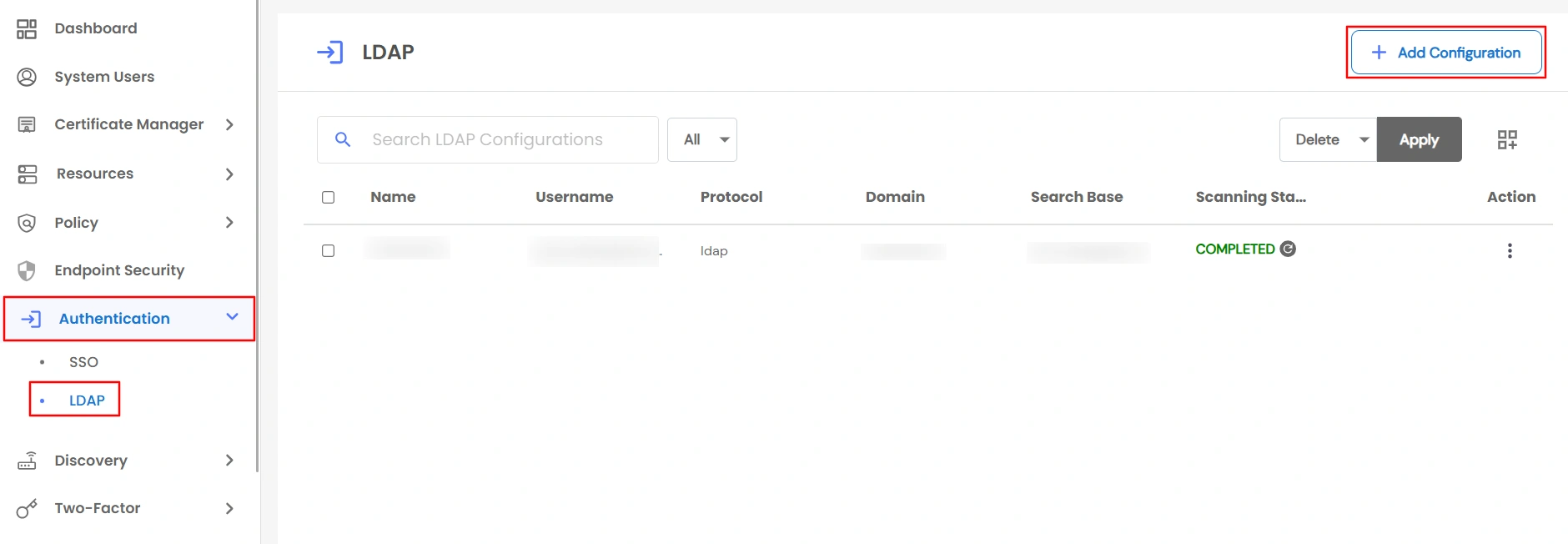
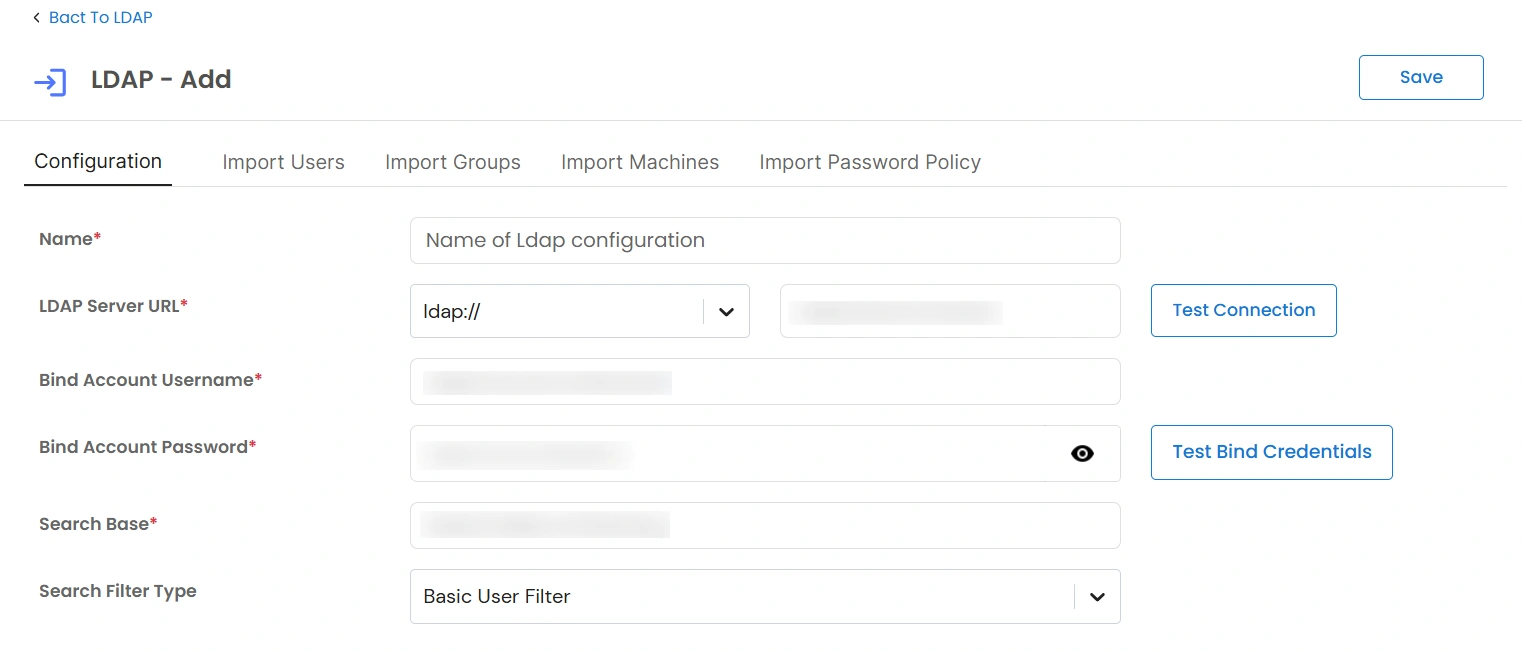
| Field | Description |
| Name | A unique name used to identify this LDAP/Active Directory configuration in PAM. |
| LDAP Server URL | The protocol and hostname or IP address of the LDAP server. |
| Bind Account Username | The LDAP service account username used to authenticate and perform directory searches. |
| Bind Account Password | The password for the bind account to securely connect to the LDAP server. | Search Base | The base Distinguished Name (DN) from which LDAP objects such as users, groups, and machines are searched. |