Need Help? We are right here!
Search Results:
×Privilege Elevation and Delegation Management (PEDM) is a security process that is a subset of Privilege Access Management, which governs how users receive elevated access to perform specific tasks across systems, applications, and endpoints. PEDM tools replace permanent administrative rights with controlled, policy-driven privilege elevation, ensuring users only get the access they need, when they need it.
The process works by granting temporary privileges for approved actions, restricting access to defined tasks or applications, and automatically revoking access once completed. PEDM also standardizes access requests, approvals, and enforcement while mitigating threats such as privilege misuse, credential theft, lateral movement, and unauthorized application execution, ensuring consistent control without disrupting workflows.
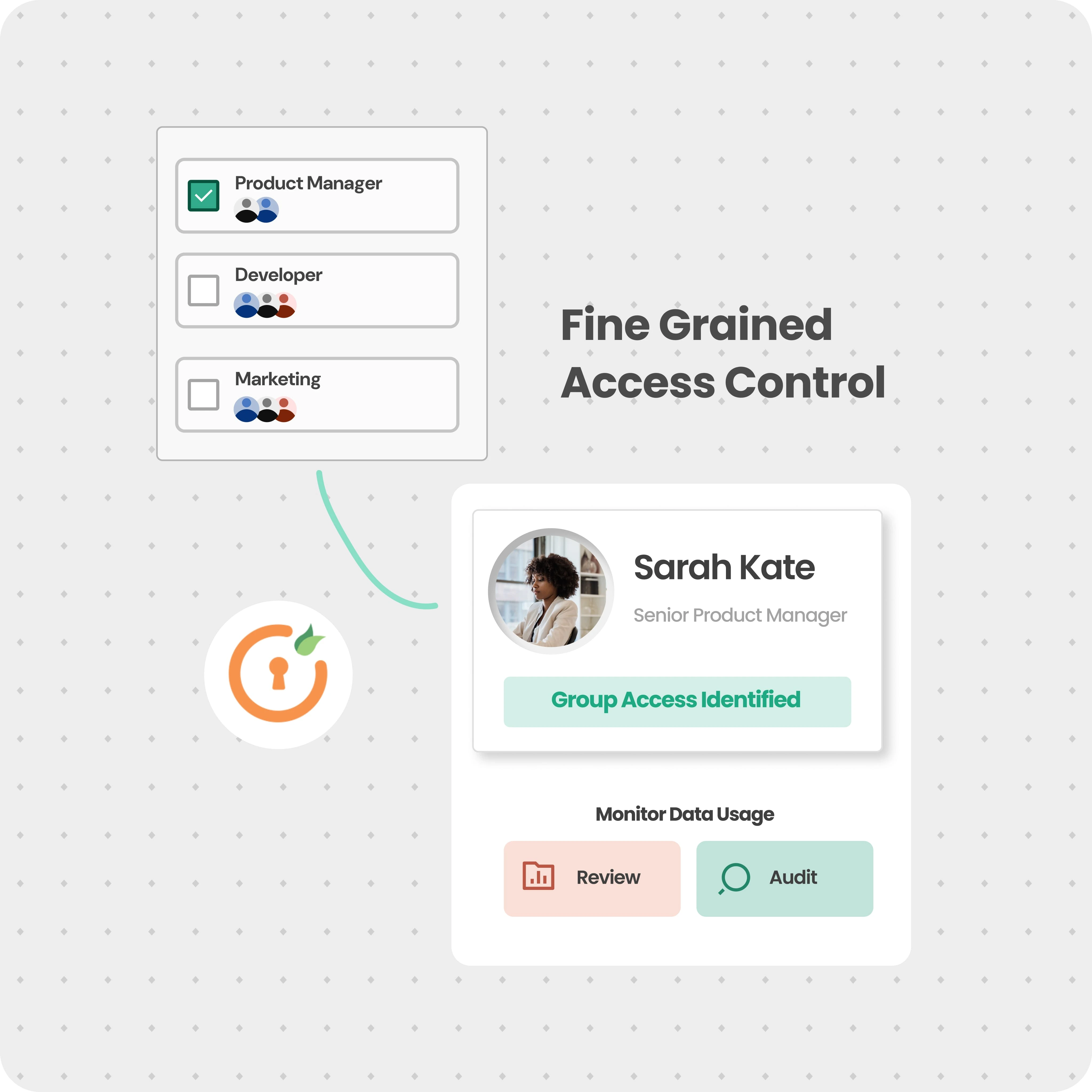
Grant elevated granular access at the application, process, or task level instead of assigning full administrative rights, ensuring precise control over user actions.
Enable temporary, time-bound access for specific tasks and automatically revoke privileges after completion to eliminate standing privileges.
Define and enforce centralized policies to control how, when, and why privilege elevation is granted across users, systems, and applications.
Control which applications can run with elevated privileges, ensuring users can securely execute required tasks without granting full system access.
Streamline access requests with structured approval workflows and enable secure delegation of privileges without compromising control.
Track and record all privileged activities with detailed logs to ensure visibility, accountability, and compliance readiness.
Grant secure, time-bound access and track every privileged action across your environment.
A user attempts to perform an action requiring elevated privileges. The request is automatically captured or initiated through a self-service workflow based on predefined policies.
The system evaluates the request against configured policies. If required, it triggers an approval workflow, ensuring only authorized and validated requests proceed.
Once approved, the user is granted time-bound, task-specific elevated access. Privileges are restricted to the required application, process, or system action.
All privileged activities are continuously monitored and logged. Access is automatically revoked after task completion, ensuring no standing privileges remain.
Aspect |
PEDM (Privilege Elevation and Delegation Management) |
PAM (Privileged Access Management) |
| Primary Focus | Controls how elevated privileges are granted for specific tasks | PManages and secures privileged accounts and credentials |
| Scope | Application, process, and task-level privilege control | Infrastructure-level access (servers, databases, network devices) |
| Access Type | Just-in-time, task-based privilege elevation | Credential vaulting, session brokering, and persistent admin accounts |
| Users | Reduces standing privileges and limits lateral movement | Secures privileged credentials and monitors high-risk sessions |
| Key Capability | Granular elevation without full admin rights | Password vaulting, session recording, and access governance |
Eliminate standing privileges and enforce least privilege with policy-based elevation across your environment.
Employees often need admin rights to install business applications, creating unnecessary security risks. PEDM allows approved applications to run with elevated privileges without granting full admin access, ensuring users can install what they need while maintaining strict control.
Developers and IT teams frequently require elevated access for debugging, configurations, or deployments. PEDM provides time-bound, task-specific privileges so they can complete critical actions without retaining permanent administrative rights.
External vendors require temporary access for system maintenance or troubleshooting, which can introduce security gaps if not controlled. PEDM enables limited, time-bound access with full monitoring, ensuring all activities are tracked and automatically revoked after completion.
Organizations struggle with users having excessive or permanent admin rights, increasing the risk of misuse and attacks. PEDM forces least privilege by granting access only when required and only for specific tasks, reducing exposure while maintaining operational efficiency.
miniOrange delivers a privilege elevation and delegation management solution that combines granular control with identity-driven access.
Make privilege decisions based on user identity, role, and access context, ensuring elevated access is granted only when truly required and appropriate.
Allow users to execute specific applications or tasks with elevated privileges instead of assigning full administrative access, reducing risk while maintaining productivity.
Automate privilege elevation using predefined policies while enabling approval-based access for sensitive actions, reducing manual intervention and delays.