Need Help? We are right here!
Search Results:
×
Applications
Customers
Worldwide Support

A PAM solution identifies the people, processes, and technology that require privileged access and specifies the policies that apply to them. This ensures maximum security for your organization with frictionless access to your employees.
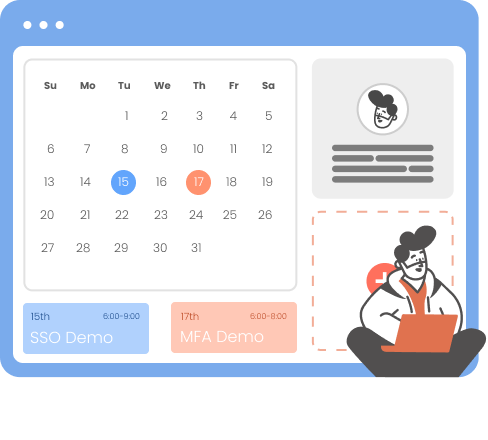
The architecture incorporates strong authentication and access control mechanisms to ensure only authorized individuals can access privileged accounts. This involves implementing SSO, Multi-factor Authentication (MFA) and access controls that enforce granular permissions and policies. By implementing strong password policies and regularly rotating passwords, robust authentication is ensured for privileged accounts. Additionally, session management capabilities are included to monitor and control privileged user sessions, with the ability to start, terminate, and record live sessions.
Implement strong passwords, MFA, & regularly rotate & manage privileged account credentials with industry-standard encryption for secure password management.
Streamline deployment with a PAM solution that cuts out individual endpoint agents. This minimizes agent-related risks, enhancing overall privileged access security.
Monitor and record privileged user sessions to detect unauthorized activities & suspicious behavior, aiding auditing, compliance, & post-incident investigations.
Conduct periodic reviews & audits of privileged access, including permissions, usage, & activities, to ensure compliance, identify risks, & make necessary adjustments.
Employ fine-grained access controls, based on the principle of least privilege, to limit & manage access to privileged accounts.
Grant temporary, on-demand (Just In Time) access to privileged accounts for a specific period, following a formal request & approval process.
Identify & inventory all privileged accounts across the organization, including those on servers, databases, network devices, & applications.
Managing remote endpoint privileges based on the policies defined with robust security controls.







I can't speak highly enough regarding miniOrange, I am totally satisfied with the process and results in every regard.
5.0

Awesome tech service, Awesome product. Overall Awesome people. This solution is very simple and easy to implement
5.0
Our Other Identity & Access Management Products