Need Help? We are right here!
Search Results:
×Advanced passwordless authentication software enables secure, seamless, and scalable access across users, devices, and applications.
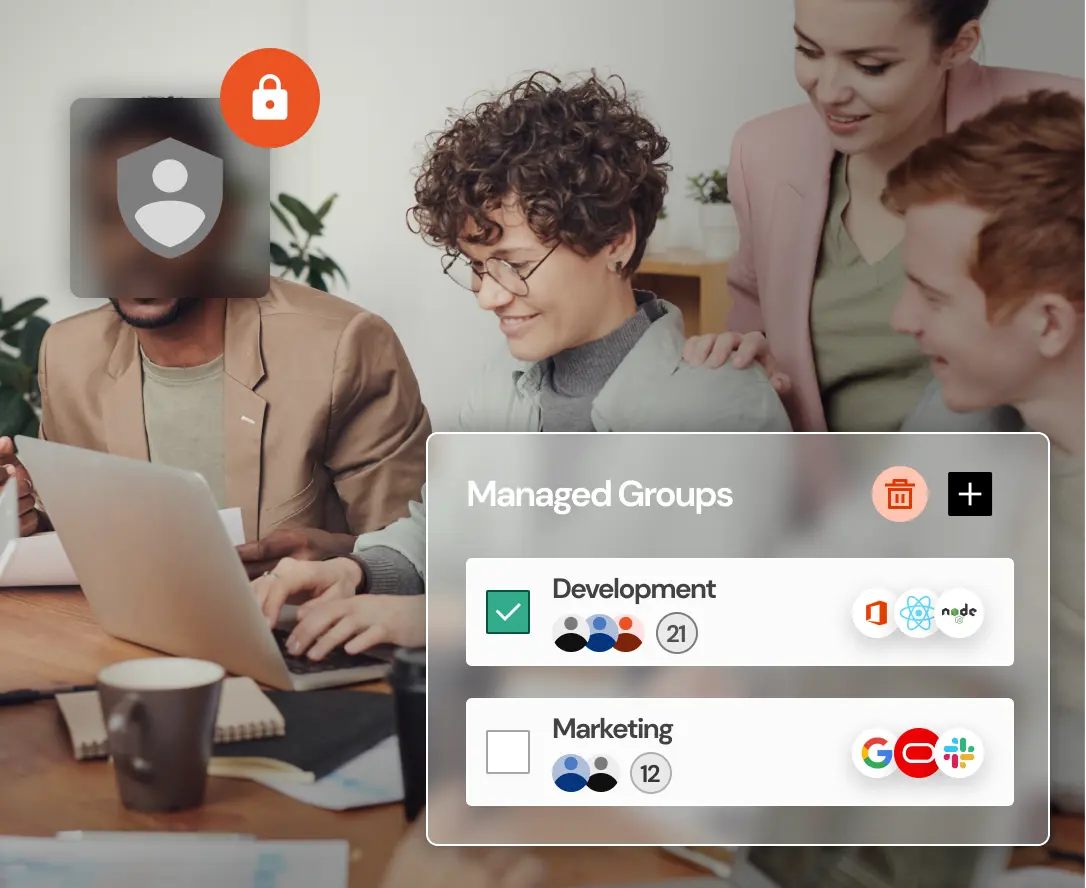
Manage authentication policies, users, and access controls from a single unified dashboard. Ensure consistent enforcement of authentication standards across applications, devices, and environments.
Apply dynamic authentication based on real-time risk signals such as user behavior, device, and location. Balance strong security with a frictionless user experience for trusted and high-risk access.
Integrate with identity providers, directories like AD/LDAP, VPNs, and cloud applications without major changes. Support standards like FIDO2 and WebAuthn for broad compatibility across systems.
Enable secure authentication across web, mobile, desktop, VPNs, and cloud environments. Deliver a consistent login experience with support for passkeys across supported devices.
Allow users to enroll devices and recover access securely without relying on IT teams. Reduce helpdesk workload while maintaining a smooth onboarding experience.
Track authentication activity with detailed logs and reporting. Maintain visibility, support compliance requirements, and monitor access across systems.
Passwordless authentication replaces traditional passwords with secure, context-aware methods to verify user identity quickly and safely.
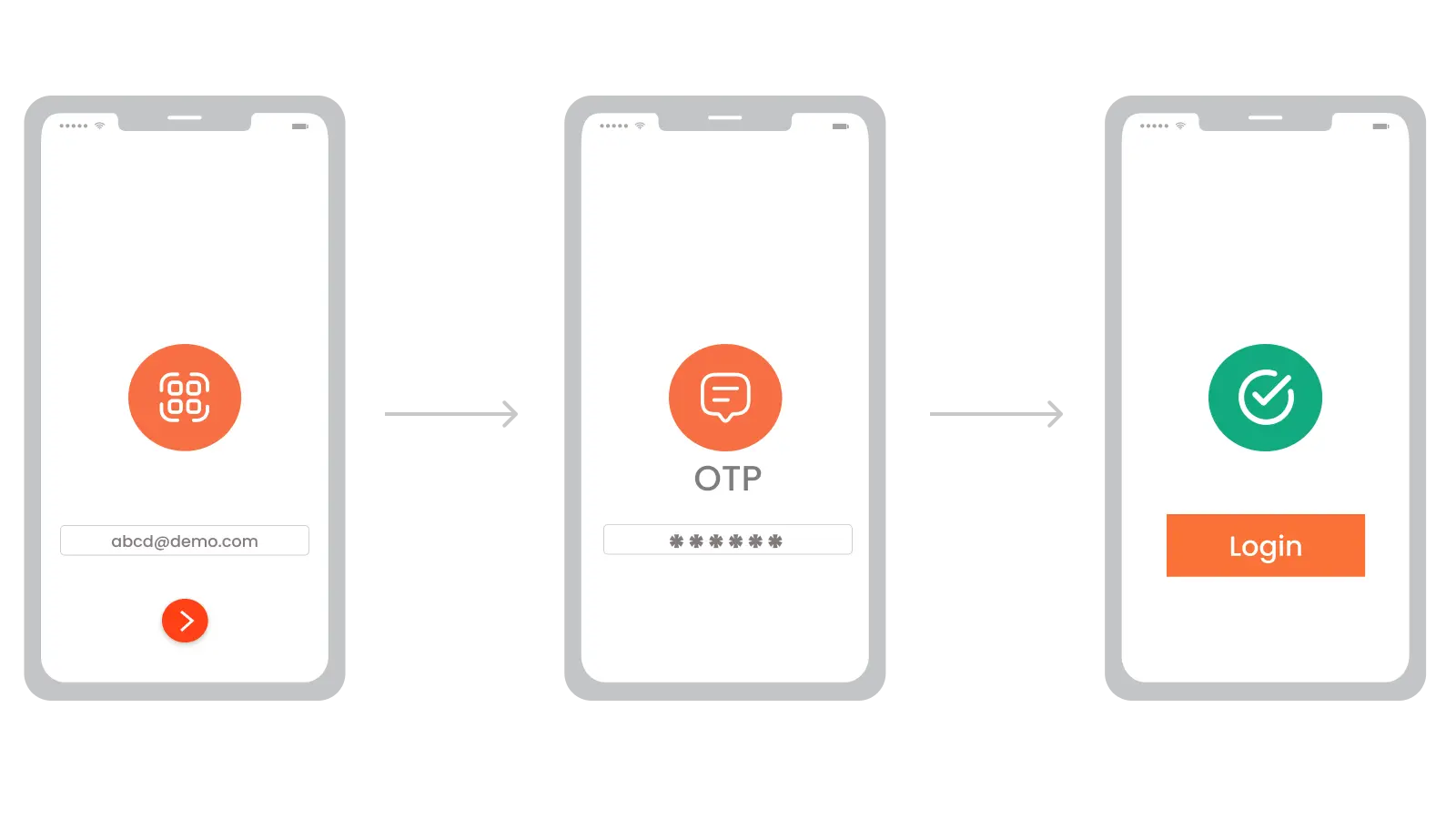
Step 1: The user initiates login without entering a password.
Step 2: The system identifies the user and evaluates context such as device, location, and risk level.
Step 3: Based on this context, the appropriate authentication method is triggered.
Step 4: Possession-based factors such as OTPs, magic links, or security keys are used when the user has a trusted device.
Step 5: Inherence-based factors such as biometrics, including fingerprint or facial recognition, verify the user’s identity.
Step 6: Access is granted once the user is securely authenticated without relying on passwords.
Support multiple passwordless authentication methods to balance security and user experience.
Authenticate users using TOTP codes generated through apps like Google Authenticator, Microsoft Authenticator, and Authy Authenticator, or via secure push notifications. This enables fast, user-friendly login with real-time approval from trusted devices.
Allow users to log in using existing social media accounts such as Google or Facebook for a seamless experience. This reduces password dependency while improving accessibility and user convenience.
Users simply enter their email and receive a secure login link instead of a password. This approach enables quick access through passwordless authentication magic link workflows while maintaining strong security.
Authenticate users using FIDO2 security keys for a highly secure and phishing-resistant login experience. This method strengthens FIDO2 passwordless authentication by eliminating reliance on passwords entirely.
Verify user identity using biometric factors such as fingerprints or facial recognition for seamless access. This ensures fast and secure authentication based on unique physical attributes.
Authenticate users using one-time codes delivered via SMS or email as a secure verification step. This provides an additional layer of protection when required without relying on traditional passwords.

Our identity and access management software supports flexible deployment options to align with your existing operational requirements.
Quickly deploy and scale IAM in a fully managed cloud environment with minimal setup and maintenance.
Maintain complete control over your infrastructure and data with on-premise deployment tailored to your security and compliance needs.
Combine cloud and on-premise environments to enable seamless identity management across distributed systems.
Use passwordless authentication to secure any customer-facing app, website, or portal.
Explore miniOrange app Integration Catalog








A modern passwordless authentication solution supports secure access across multiple use cases.
Secure employee access across devices and enterprise systems.

Deliver seamless and secure user experiences for customers.
Protect sensitive systems with advanced authentication controls.

miniOrange delivers a secure, scalable, and enterprise-ready passwordless authentication platform designed to simplify access while strengthening security.
Manage authentication, access policies, and user identities from a single platform, giving you complete visibility across users, devices, and applications. This unified approach reduces tool sprawl and simplifies security operations without compromising control.
Secure both legacy applications and modern cloud environments with a solution designed for flexibility. Passwordless authentication can be extended seamlessly across on-premise and cloud systems without disrupting existing workflows.
Integrate effortlessly with your existing infrastructure, applications, and identity providers to maintain continuity. The solution is designed for quick deployment, eliminating the need for complex system changes.
Protect user identities with advanced authentication controls designed to prevent unauthorized access. The platform secures critical systems across environments while reducing risks associated with password-based attacks.
Ensure your passwordless authentication solution aligns with global security frameworks and regulatory requirements.
Align authentication practices with NIST 800-63B guidelines to ensure secure and reliable identity verification.
Protect user data and ensure privacy compliance across applications and systems.
Secure healthcare data with strong authentication controls and access policies.
Protect payment systems with secure and compliant authentication methods.