Need Help? We are right here!
Search Results:
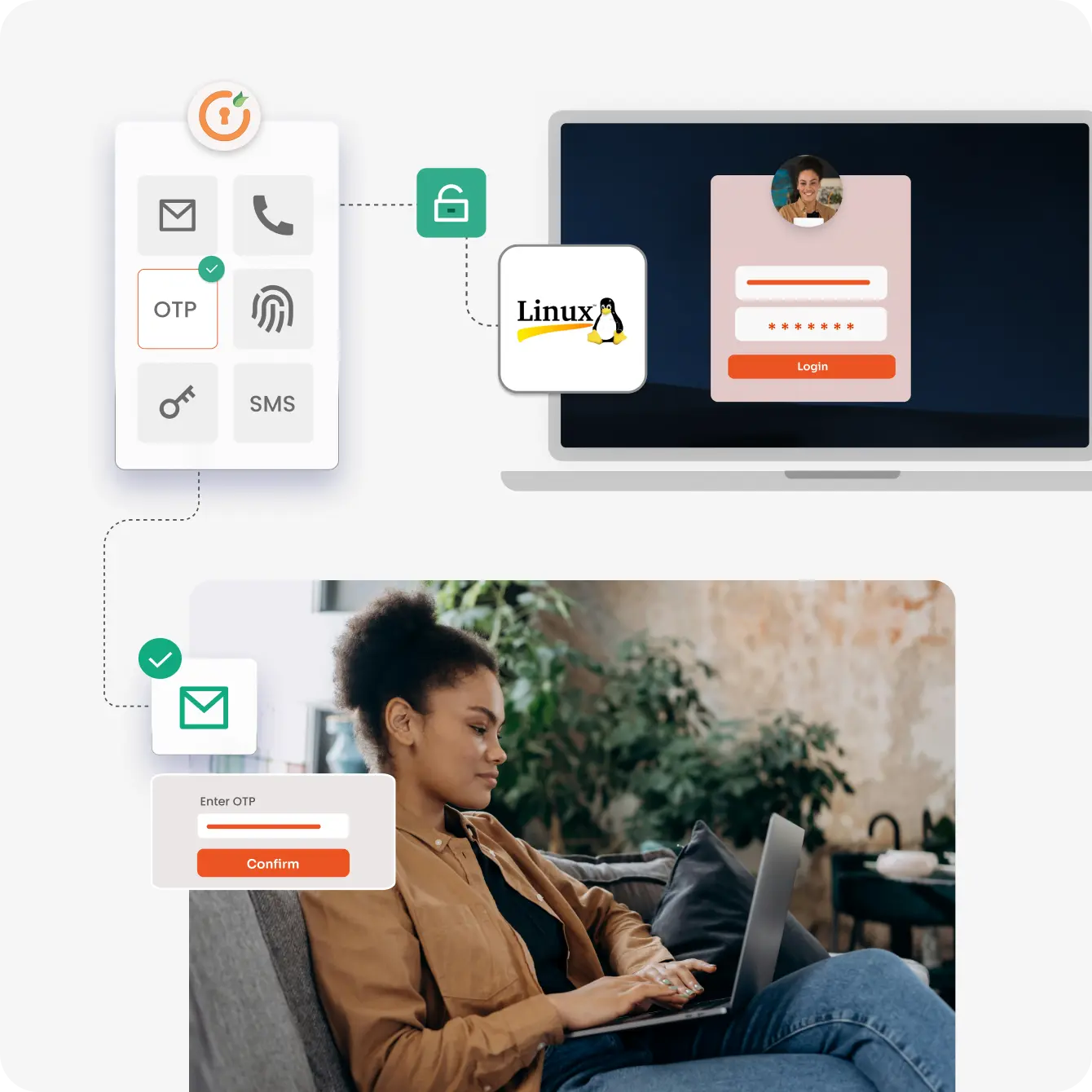
×Linux Multi-Factor Authentication can be utilized to protect against Password-based attacks. By enabling MFA for local console logins & SSH Connections, identity can be verified before granting access, making it harder for people who should not be able to access your linux device and accounts.
With miniOrange Linux MFA, you can add an extra layer of protection to your Linux servers, workstations, and cloud instances, ensuring that only authorized users can access critical systems and data.
Secure remote access to your Linux servers by enabling MFA for SSH. miniOrange makes it easy to configure SSH protection, ensuring that only verified users can access your systems remotely.
Integrating miniOrange with the Pluggable Authentication Module (PAM) framework allows you to enforce MFA across various Linux services like SSH, Sudo, and more. With a straightforward setup, you can add MFA to critical system functions, significantly enhancing your security posture.
miniOrange doesn’t just protect command-line interfaces; it also provides MFA options for graphical desktop environments like GNOME and KDE. Whether your users prefer a GUI or a terminal, miniOrange has you covered.
Our centralized management console allows you to deploy, monitor, and manage MFA across all your Linux systems from a single location. Easily set policies, manage users, and ensure compliance with security standards.
Stay on top of your security with miniOrange's comprehensive reporting and logging features. Monitor login attempts, MFA successes and failures, and generate detailed reports for security audits and compliance requirements.
Organizations subject to regulatory requirements can leverage miniOrange MFA to meet compliance standards. Our comprehensive logging and reporting features support security audits and help demonstrate adherence to strict access control policies.
Begin by installing miniOrange MFA on your Linux distribution. Our Linux MFA detailed guide provide step-by-step instructions for different Linux environments, ensuring a smooth setup process.
Configure miniOrange SSH (MO-SSH) modules, and other Linux services to enforce MFA where it's needed most.
Enable users to enroll in MFA by setting up their preferred authentication method. The process is straightforward and user-friendly, ensuring high adoption rates.
After setup, test the configuration to ensure everything works as expected. Once verified, deploy the MFA solution across your environment for enhanced security.
Implementing miniOrange MFA for SSH access ensures that only authenticated users can remotely access your Linux servers. This layer of security is vital for protecting against unauthorized logins and potential breaches.
For enterprises using Linux desktops, miniOrange provides MFA solutions that safeguard user logins in graphical environments. This ensures that only authorized personnel can access sensitive workstations.
Identity solutions from miniOrange can be easily deployed in your organization's existing environment.
*Please contact us to get volume discounts for higher user tiers.
Protect all Active Directory logins with MFA Security. Prevent unauthorized access to all servers by enabling MFA.
Secure your Windows RDP logons, RD Gateway & SSH logins with Multi-Factor Authentication.
Enable MFA on your VPN connections Like Fortinet, Cisco, SonicWall, PaloAlto, etc.
Prevent unauthorized access to OWA (Outlook on the Web) & RD Web connections.
Enable SSO/MFA for all Office 365 apps on the cloud (Supporting SAML, OAuth, JWT, etc.)
Secure your Virtual Desktop Infrastructure (VDI) (like Citrix, VMWare, etc.) with MFA solution.





I can't speak highly enough regarding miniOrange, I am totally satisfied with the process and results in every regard.
5.0

Awesome tech service, Awesome product. Overall Awesome people. This solution is very simple and easy to implement
5.0