Implementing Single Sign-On (SSO) across multiple applications is a growing priority for modern enterprises managing complex digital ecosystems. As organizations adopt more SaaS platforms, internal tools, and cloud services, handling separate authentication for each system increases security risks, operational overhead, and user friction.
SSO implementation solves this by enabling centralized authentication, allowing users to log in once and securely access multiple applications without repeated sign-ins. However, implementing SSO is not just a configuration task. It requires careful planning around protocols, identity providers, application integration, and session management.
This guide covers how to implement SSO step by step, along with best practices, architecture insights, and common challenges to help you build a secure and scalable authentication framework.
What is Single Sign-On (SSO)?
Single Sign-On (SSO) is an authentication mechanism that allows users to log in once and access multiple applications without re-entering credentials.
In a traditional authentication model, each application independently verifies user identity, requiring separate login credentials. This fragmented approach increases administrative overhead and introduces security risks due to password reuse and weak credential management.
With Single Sign-on(SSO), authentication is handled by a centralized system known as an Identity Provider (IdP). Once a user successfully authenticates, the IdP generates a secure token that is shared with connected applications. These applications trust the IdP and grant access without requiring additional logins.
This centralized model simplifies access management while enabling organizations to enforce consistent authentication policies across all systems.
Why is Single Sign-On (SSO) Important for Modern Enterprises?
Single Sign-On is important because it enhances security, improves user experience, and simplifies access management across multiple systems.
Eliminates Password Fatigue
Users often struggle to manage multiple credentials across various applications. This leads to frequent password resets, reliance on insecure storage methods, or reuse of weak passwords. Single Sign-On reduces this burden by allowing users to maintain a single set of credentials, improving usability and reducing friction in daily workflows.
Reduces Security Risks
Password-based authentication remain one of the most common attack vectors. By centralizing authentication, SSO minimizes the risk of credential reuse and enables stronger authentication solutions such as multi-factor authentication (MFA). This significantly reduces the likelihood of unauthorized access.
Improves Productivity
Repeated login prompts disrupt workflow and waste time. SSO solution eliminates redundant authentication steps, allowing users to seamlessly transition between applications. This improves efficiency and enables employees to focus on core tasks rather than addressing issues.
Supports Compliance and Auditing
Organizations must meet strict regulatory requirements related to data access and security. SSO provides centralized logging and access control, making it easier to monitor user activity, generate audit reports, and demonstrate compliance with industry standards.
How SSO Implementation Works
Single sign-on (SSO) works by creating a trust relationship between an identity provider and multiple applications, using secure tokens to authenticate users across systems.
Identity Provider (IdP)
The Identity Provider is responsible for verifying user credentials and managing identity data. It acts as the central authority in the authentication process. When a user logs in, the IdP validates their identity and generates an authentication token that can be used across multiple applications.
Service Provider (SP)
Service Providers are the applications or services that rely on the IdP for authentication. Instead of maintaining their own authentication systems, they trust the IdP to verify user identity and grant access accordingly.
Authentication Flow
The SSO authentication flow begins when a user attempts to access an application. The application redirects the user to the IdP for authentication. Once the user successfully logs in, the IdP generates a secure token and sends it back to the application. The application validates the token and grants access without requiring additional credentials.
This process happens quickly and seamlessly, often without the user noticing the multiple steps involved.
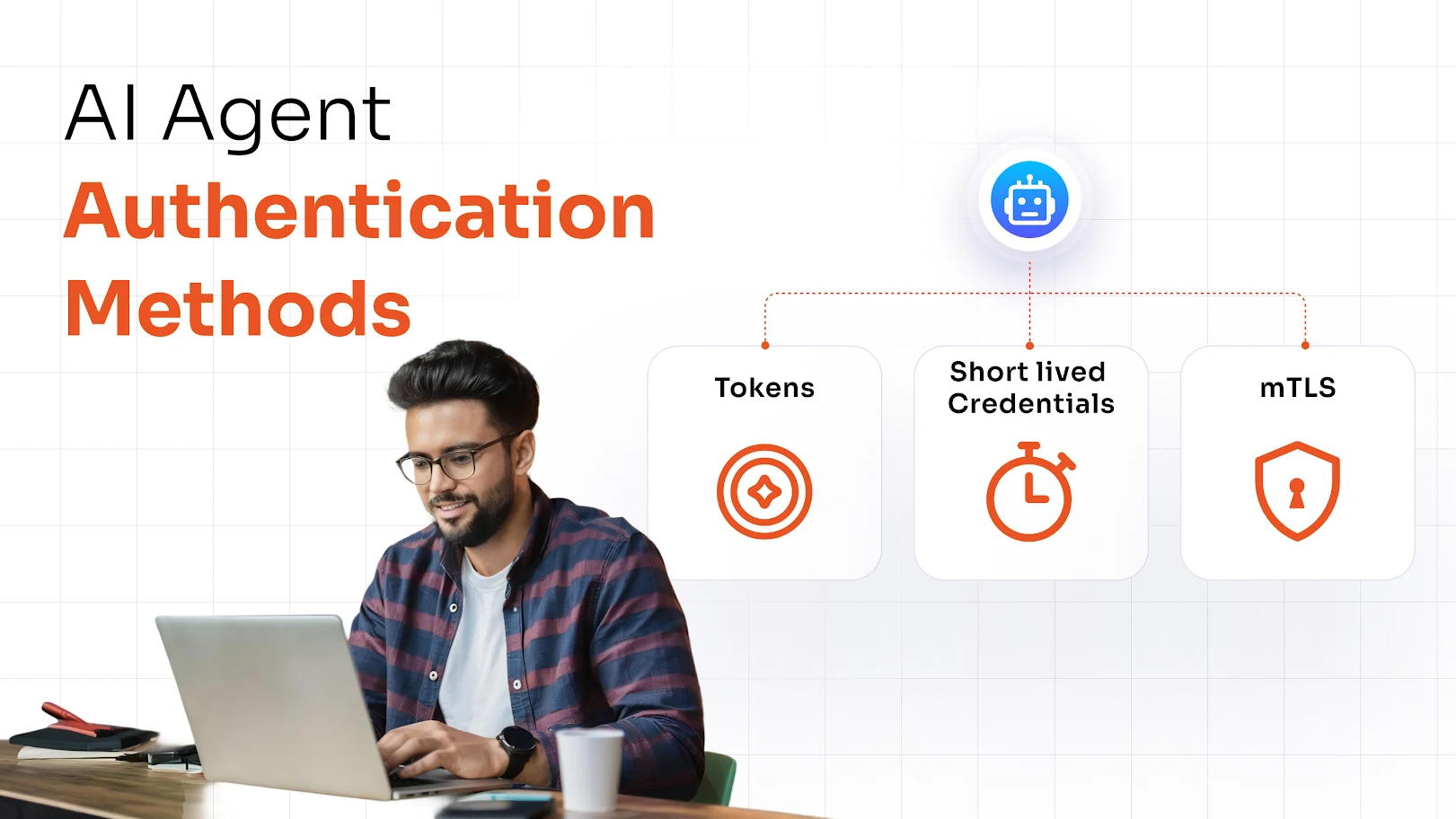
Tokens and SSO Protocols
SAML (Security Assertion Markup Language)
SAML is widely used in enterprise environments for secure authentication. It uses XML-based messages to exchange authentication data between the IdP and service providers.
OAuth 2.0
OAuth is primarily an authorization framework that allows applications to access resources on behalf of a user. While not strictly an authentication protocol, it plays a key role in modern identity systems.
OpenID Connect (OIDC)
OIDC is an authentication layer built on top of OAuth 2.0. It is commonly used for modern web and mobile applications due to its simplicity and flexibility.
SSO Implementation Steps
To implement SSO, organizations must follow a structured approach that includes selecting the right tools, integrating systems, and configuring secure authentication flows.
1. Define Business and Security Requirements
Start by identifying the applications that need to be integrated, the types of users who will access them, and the level of security required. Consider compliance requirements, access control policies, and user experience expectations.
2. Choose the Right SSO Protocol
Selecting the appropriate protocol is critical for compatibility and performance. SAML is typically used for enterprise SaaS applications, while OAuth and OIDC are better suited for modern web and mobile applications.
3. Select an Identity Provider (IdP)
Choose an IdP that supports your organization’s scalability, integration needs, and security requirements. The IdP should offer features such as MFA, directory integration, and centralized policy management.
4. Configure Service Providers (Applications)
Each application must be configured to trust the IdP. This involves setting up metadata, certificates, and endpoints required for secure communication.
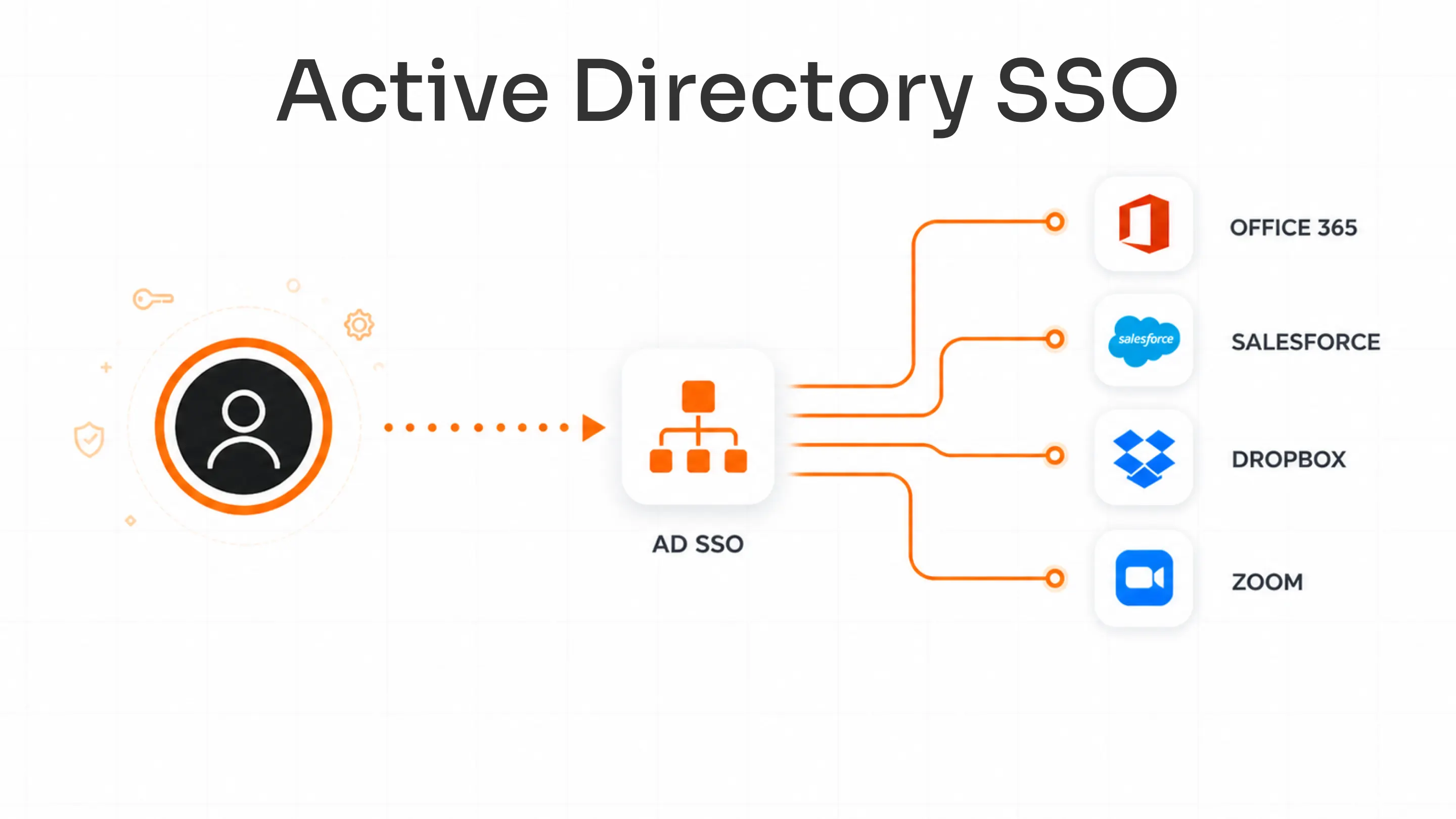
5. Integrate User Directories
User identities are typically stored in directories such as Active Directory or LDAP. Integrating these directories ensures that user data is synchronized and consistently managed across systems.
6. Configure Authentication Flow
Define how users will authenticate, how tokens will be generated, and how sessions will be managed. This step ensures a seamless and secure login experience.
7. Test SSO Implementation
Before deployment, thoroughly test the system to ensure that authentication works correctly across all applications. Validate token handling, session management, and error scenarios.
8. Deploy, Monitor, and Optimize
Roll out SSO gradually and monitor its performance. Use logs and analytics to identify issues, optimize configurations, and improve security over time.
Implementation Tip
Start with a small group of applications and users before scaling across the organization. This phased approach helps identify potential issues early and reduces deployment risks.
How to Implement SSO in Web Applications
Implementing SSO in web applications involves configuring authentication protocols, managing sessions, and enabling secure communication between systems. Below is an overview of SP-initiated vs IdP-initiated SSO implementation.
SP-Initiated vs IdP-Initiated
In SP-initiated SSO, the authentication process begins when a user tries to access an application. The application redirects the user to the IdP for authentication. In IdP-initiated SSO, the user starts from the identity provider and selects an application to access.
Both approaches are widely used, and the choice depends on the user experience and system design.
Token Exchange
Token exchange is a critical part of any SSO solution. Once the user is authenticated, the IdP generates a token that contains identity information. This token is securely transmitted to the application, which verifies it before granting access.
Session Management
Session management ensures that users remain authenticated across multiple applications. Proper session handling prevents unnecessary logins while maintaining security through session expiration and renewal mechanisms.
Browser Redirects
SSO relies on secure browser redirects to facilitate communication between the IdP and applications. These redirects must be properly configured to prevent vulnerabilities such as token leakage or interception.
SSO Implementation Best Practices
Implementing SSO effectively requires a combination of strong security practices, proper configuration, and continuous monitoring.
Enable Multi-Factor Authentication (MFA)
Multi-factor Authentication (MFA) adds a layer of security by requiring users to verify their identity using multiple factors. This significantly reduces the risk of unauthorized access.
Follow Least Privilege Access
Users should only have access to the resources necessary for their roles. Implementing least privilege reduces the potential impact of compromised accounts.
Secure Token Handling
Tokens should be encrypted, validated, and stored securely. Improper handling of tokens can lead to serious security vulnerabilities.
Monitor Sessions and Logs
Continuous monitoring helps detect unusual behavior and potential threats. Logs provide valuable insights for troubleshooting and compliance.
Ensure Protocol Compatibility
Verify that all applications support the chosen SSO protocols. Compatibility issues can disrupt authentication and create security gaps.
Conduct Regular Audits
Periodic audits help identify misconfigurations, outdated policies, and potential vulnerabilities, ensuring that the SSO system remains secure and effective.
SSO Security Benefits
Single Sign-On enhances security by centralizing authentication and reducing reliance on multiple credentials. By consolidating authentication into a single system, organizations can enforce stronger policies and gain better visibility into user activity. This reduces the attack surface and simplifies security management.
Additionally, SSO enables faster detection of suspicious behavior, as all authentication events are logged and monitored centrally. This makes it easier to respond to potential threats and maintain compliance with regulatory standards.
Common Challenges in SSO Implementation
SSO implementation can present challenges related to integration, compatibility, and system reliability.
Legacy Application Integration
Older applications may not support modern authentication protocols, requiring custom integrations or additional tools to enable Single Sign-On (SSO) functionality.
Protocol Mismatch
Different applications may use different authentication standards, making it difficult to create a unified system without careful planning.
Single Point of Failure
Since SSO relies on a central identity provider, any downtime can impact access to all connected applications. High availability and redundancy are essential.
User Provisioning Complexity
Managing user identities across multiple systems requires synchronization and automation to ensure consistency and accuracy.
Should You Build or Buy an SSO Solution?
Choosing between building or buying an SSO solution depends on your organization’s resources, security expertise, and long-term scalability needs.
Building an SSO Solution
Building an in-house SSO system gives organizations full control over authentication logic and integrations. However, it requires significant engineering effort and long-term commitment to security and maintenance.
Development Time and Complexity
Developing SSO from scratch involves implementing authentication protocols such as SAML, OAuth, and OIDC, along with secure token handling and session management. This process can take several months, especially when integrating multiple applications with varying requirements.
Security Ownership and Risk
When building SSO internally, the responsibility for security lies entirely with your organization. This includes protecting against token misuse, replay attacks, session hijacking, and misconfigurations. Keeping up with evolving security standards and compliance requirements adds additional overhead and risk if not managed properly.
Maintenance and Scalability Challenges
As your application ecosystem grows, maintaining integrations becomes increasingly complex. Updates to APIs, protocols, or applications can break authentication flows, requiring continuous monitoring and development effort. Scaling the system to support more users and applications also demands infrastructure planning and optimization.
Buying an SSO Solution
Buying a pre-built SSO solution allows organizations to implement centralized authentication faster while reducing the complexity of managing identity systems internally.
Faster Deployment and Time-to-Value
Pre-built SSO platforms are designed for quick implementation. Organizations can integrate applications using pre-configured connectors and deploy SSO in a matter of days or weeks instead of months. This significantly accelerates time-to-value and reduces dependency on internal development cycles.
Built-in Security and Protocol Support
Most SSO solutions natively support industry-standard protocols like SAML, OAuth, and OIDC. They also include built-in security features such as MFA, adaptive authentication, and session monitoring. This ensures that authentication is handled securely without requiring deep in-house expertise.
Scalability and Integration Ecosystem
SSO vendors typically offer extensive integration libraries, enabling organizations to connect thousands of applications without custom development. As business needs evolve, new applications can be added with minimal effort, making it easier to scale authentication across the organization.
SSO Implementation with miniOrange
SSO implementation often involves challenges such as integrating diverse applications, managing authentication protocols, and maintaining consistent security policies.
miniOrange SSO provides a unified approach by supporting a wide range of integrations and enabling centralized authentication. This helps organizations simplify implementation while maintaining flexibility and scalability.
Final Thoughts
SSO implementation is a critical component of modern identity security strategies. By understanding how SSO works, following structured implementation steps, and applying best practices, organizations can create a secure and seamless authentication experience.
A well-implemented SSO solution not only simplifies access but also strengthens security and prepares organizations for future identity management challenges.
FAQs
How to implement SSO?
To implement SSO, choose an identity provider, select a protocol such as SAML or OIDC, integrate applications, configure authentication flows, and test deployment.
What is the best SSO protocol?
SAML is commonly used for enterprise applications, while OAuth and OIDC are preferred for modern web and mobile environments.
How long does SSO implementation take?
SSO implementation typically takes from a few days to several weeks, depending on the number of applications and complexity.
Is SSO secure?
SSO is secure when combined with multi-factor authentication, secure token handling, and proper configuration.
How to implement SSO in web applications?
Use OIDC or OAuth, configure token exchange, manage sessions securely, and implement browser redirects between the application and identity provider.

Leave a Comment