Identity and Access Management (IAM) is the security backbone of every modern organization. According to the Verizon Data Breach Investigations Report, over 80% of breaches involve compromised or misused credentials - and IAM is the primary control that stops them. Whether your team works from an office, at home, or across continents, a robust IAM system ensures the right people access the right resources, at the right time, for the right reasons - and that everyone else stays out.
This guide covers everything you need to know about identity and access management: what it is, how an IAM system works, its core components, deployment options, supported protocols, compliance frameworks, and how to choose the right IAM product for your organization.
What is IAM (Identity and Access Management)?
Identity and Access Management (IAM) is a framework of policies, processes, and technologies that enables organizations to manage digital identities and control user access to critical information and systems. It ensures the right people - and only the right people - have appropriate access to technology resources at the right times and for the right reasons.
IAM combines identity management (creating and governing user identities) with access management (controlling what those identities can do). This comprehensive approach helps organizations maintain security, achieve regulatory compliance, and streamline user experiences across on-premises, cloud, and hybrid environments.
The Core Concept of Digital Identity
A digital identity is the online representation of a person, device, application, or service in a digital environment. Every entity that needs to access a system has a digital identity - and IAM is what manages and secures those identities at scale.
Primary components of a digital identity
- Personal identifiers: names, email addresses, usernames, employee IDs
- Digital credentials: passwords, security tokens, digital certificates
- Biometric data: fingerprints, facial recognition, voice prints
- Device identifiers: IP addresses, device IDs, hardware fingerprints
- Behavioral patterns: login times, usage history, interaction patterns
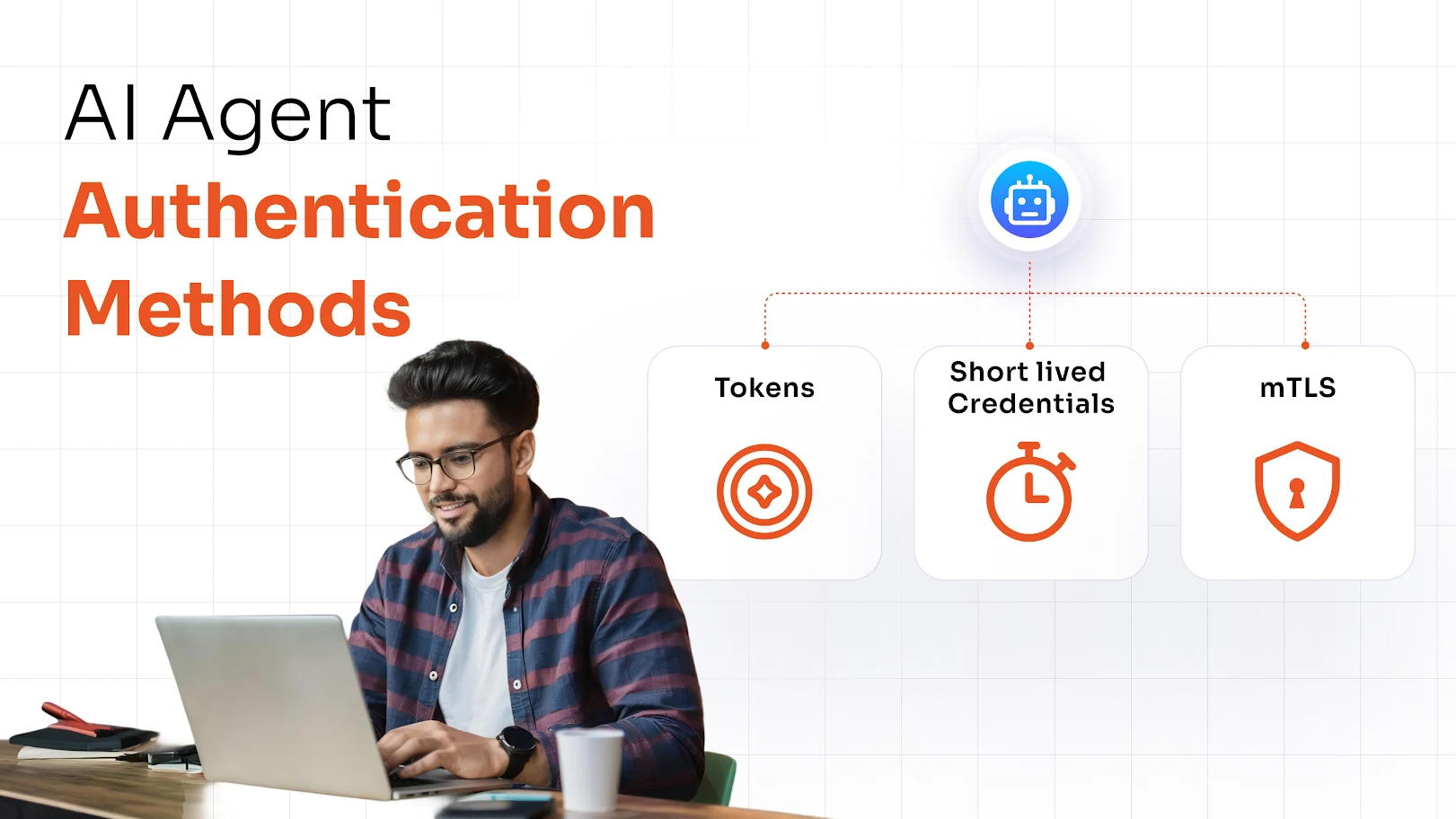
Human vs. Non-Human IdentitiesModern IAM goes beyond employees. Machine identities - including service accounts, API tokens, IoT devices, bots, and microservices - now outnumber human identities in most organizations. A complete IAM system manages both.
Challenges Organizations Face Without an IAM System
Without a centralized IAM system, organizations struggle with fragmented access controls, growing security gaps, and compliance failures. Here are the key risks:
Cybersecurity vulnerabilities
Unmanaged identities are the leading entry point for attackers. Credential theft, privilege escalation, and lateral movement all thrive when access is ungoverned. The IBM Cost of a Data Breach Report 2024 found the average breach costs $4.88 million - and identity-related attacks are the most common vector.
Operational inefficiencies
Manual provisioning and deprovisioning of accounts creates IT overhead, delays, and costly errors. When an employee changes roles or leaves, ad hoc access removal processes leave dangerous gaps - commonly known as orphaned accounts or access creep.
Compliance and governance failures
Regulations like GDPR, HIPAA, SOX, and PCI DSS require strict access controls and audit trails. Without IAM, proving compliance becomes nearly impossible - exposing organizations to significant legal and financial risk.
Application sprawl and shadow IT
When teams adopt cloud apps without centralized oversight, inconsistent authentication policies and security gaps proliferate across the organization. IAM provides the centralized control layer to address this.
Identity Management vs. Access Management - What's the Difference?
These two terms are often used interchangeably, but they serve distinct functions:
| Aspect | Identity Management | Access Management |
|---|---|---|
| Core question | "Who are you?" | "What can you access?" |
| Focus | Creating, managing, and governing digital identities throughout their lifecycle | Controlling permissions, authorization policies, and resource access |
| Key functions | User provisioning, authentication, profile management | RBAC, ABAC, SSO, MFA, policy enforcement |
| Security goal | Prevent unauthorized identity creation or compromise | Prevent unauthorized access to systems and data |
IAM vs. Identity Management - Key Differences
| Aspect | Identity Management | IAM (Identity & Access Management) |
|---|---|---|
| Scope | Focuses solely on managing digital identities, user accounts, and authentication | Combines identity management + access management into one security framework |
| Components | Provisioning, authentication, profile management | SSO, MFA, RBAC, IGA, PAM, governance |
| Security focus | Verifying who you are | Who you are + what you can do after login |
| Best for | Authentication-only needs | Full enterprise security and compliance |
How Does an IAM System Work?
An IAM system combines technology, policies, and automated workflows to manage identity and control access across an organization. Here is the typical IAM workflow:
1. Identity creation and management
When a new user, device, or application joins the organization, IAM creates a unique digital identity stored in a centralized directory. This identity includes attributes like name, role, department, and access level. As roles change, the IAM system updates attributes and access rights in real time.
2. Authentication - verifying who you are
Authentication confirms that users are who they claim to be. IAM systems support multiple authentication methods including passwords, biometrics, smart cards, and multi-factor authentication (MFA). MFA is now a baseline requirement for any serious IAM deployment, requiring two or more independent verification factors before granting access.
3. Authorization - determining what you can access
Once authenticated, IAM applies predefined policies to determine which resources a user may access. These boundaries are enforced through role-based access control (RBAC), attribute-based access control (ABAC), and the principle of least privilege.
4. Access control enforcement
IAM continuously applies these policies at the session level - not just at login. This is the foundation of Zero Trust security: every access request is evaluated independently, regardless of the user's network location.
5. Monitoring and auditing
IAM systems log all access events, flag anomalous behavior, and generate audit-ready reports. This supports incident response, forensic investigation, and regulatory compliance by providing a complete record of who accessed what and when.
6. Integration with applications and directories
IAM integrates with your existing apps, cloud services, and directories using standard protocols - SAML, OAuth 2.0, OpenID Connect, SCIM, and LDAP. miniOrange IAM offers 6,000+ pre-built app integrations covering cloud-native and legacy environments.
| Real-world example: IAM in a healthcare organization A hospital network uses IAM to manage access across EHRs, billing systems, and patient portals. Doctors get read/write access to patient records; nurses get read-only access to care plans; billing staff access financial systems only. SSO + MFA is enforced at login. All access is logged. When a staff member leaves, IAM automatically revokes access across every system - instantly. |
|---|
The Four Core Pillars of an IAM System
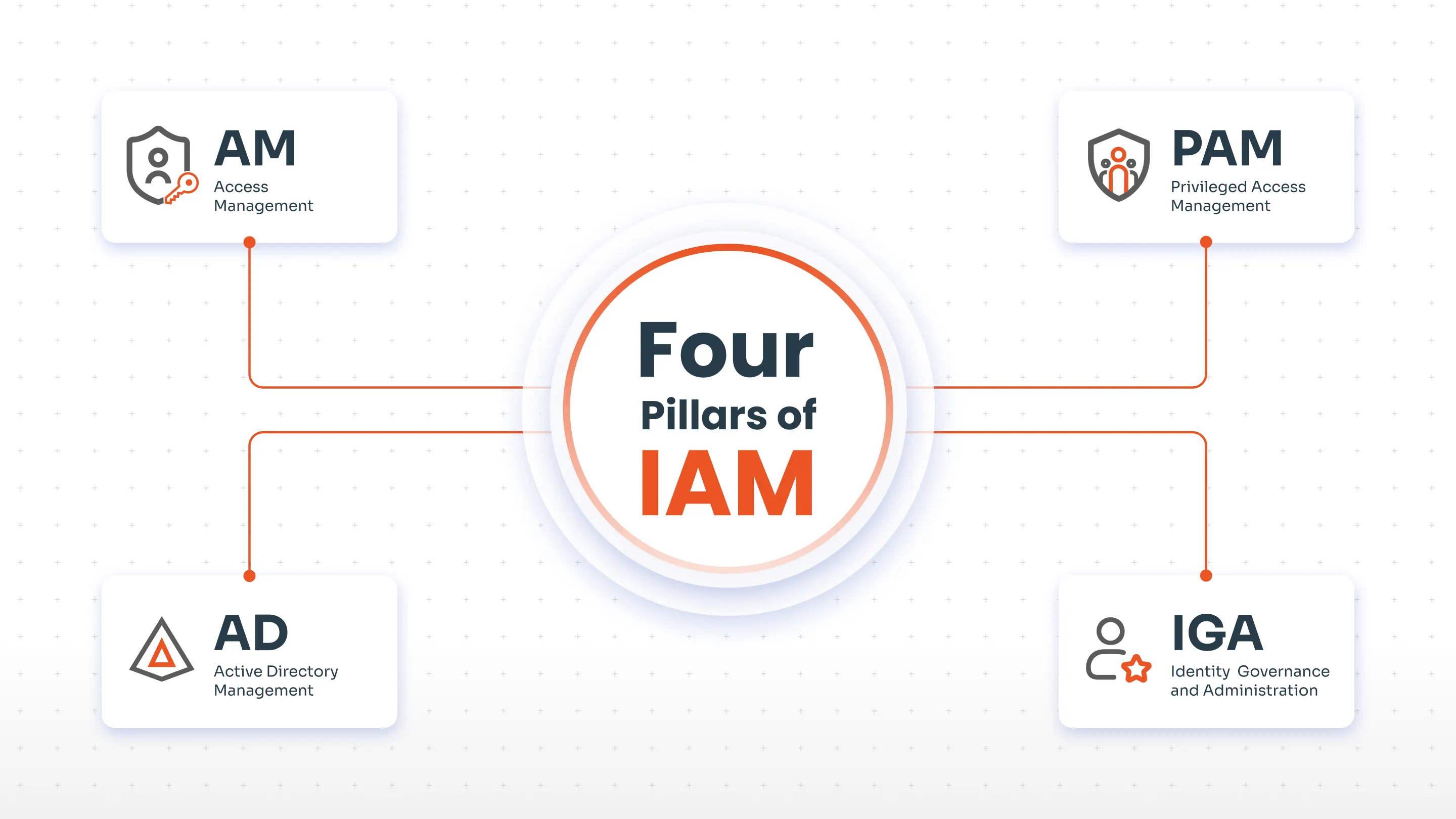
1. Identity Governance and Administration (IGA)
IGA governs the complete identity lifecycle - user provisioning, deprovisioning, access certification, and role management. It ensures users have the right access at the right time, and automates compliance audits and access reviews. Without IGA, organizations accumulate excessive permissions and orphaned accounts over time.
2. Access Management (AM)
Access Management controls how users authenticate and gain access to systems. Key technologies include Single Sign-On (SSO), Multi-Factor Authentication (MFA), and Role-Based Access Control (RBAC). The goal is secure, seamless access that does not slow users down while protecting sensitive resources.
3. Privileged Access Management (PAM)
Privileged Access Management (PAM) secures accounts with elevated permissions - system administrators, database owners, C-suite executives. PAM enforces strict controls, session monitoring, just-in-time access, and detailed audit logging to prevent privilege misuse.
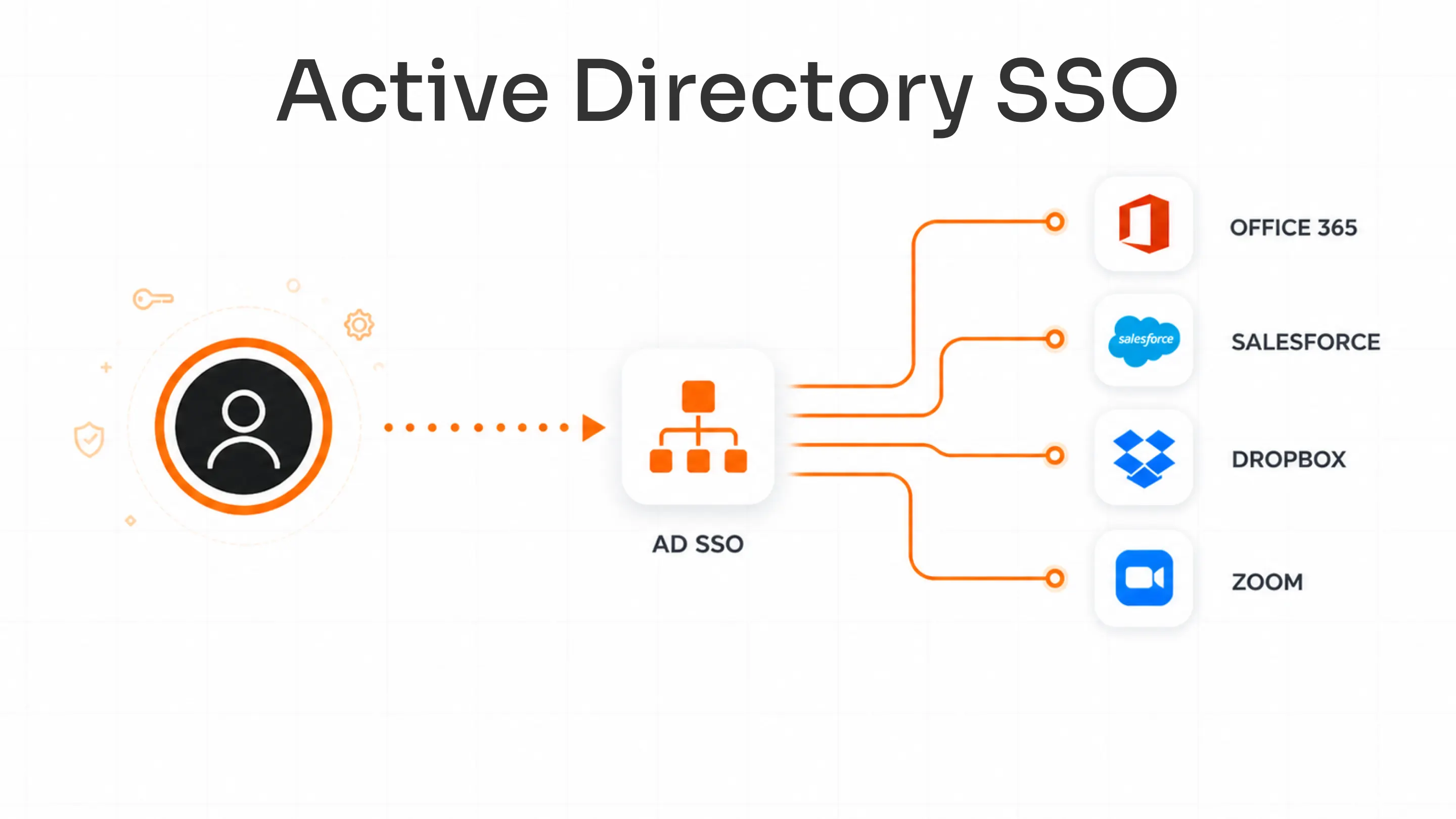
4. Directory Services and Identity Repositories
Directory services like Microsoft Active Directory and LDAP serve as the central store for identity data. They authenticate users, manage groups, and enforce access policies across platforms - the foundational infrastructure all other IAM pillars depend on.
Key Components of Identity and Access Management

User authentication
IAM verifies the identity of users, devices, and applications before granting access. Authentication methods range from passwords and PINs to biometrics, hardware tokens, and passwordless authentication via passkeys.
User authorization
Once authenticated, IAM enforces what that identity is allowed to do. Role-based and attribute-based access control policies ensure users interact only with the systems and data relevant to their function.
Account administration
IAM automates account lifecycle management - creation, modification, and removal. User lifecycle management workflows triggered by HR events eliminate manual errors and prevent access creep.
Access governance and compliance
IAM continuously monitors, records, and audits access events. Access governance includes periodic access reviews, segregation of duties (SoD), and policy enforcement - all critical for regulatory compliance.
Types of IAM Based on Identity
Workforce IAM
Workforce IAM manages internal identities - employees, contractors, partners. It integrates tightly with HR systems to automate onboarding and offboarding, and uses SSO, MFA, and RBAC to secure enterprise applications.
Customer IAM (CIAM)
Customer Identity and Access Management (CIAM) is designed for external users: customers, consumers, and end users. It prioritizes scalability, user experience, and data privacy - supporting millions of users across diverse devices with social login, progressive profiling, and consent management.
Machine and non-human identity management
This is the fastest-growing IAM domain. Service accounts, API tokens, IoT devices, bots, RPA agents, and microservices all have identities that need to be managed, secured, and audited. Machine identities now outnumber human identities in most enterprise environments, making non-human identity management (NHI) a critical part of any complete IAM strategy.
IAM and Zero Trust Security
Zero Trust is a security model built on one principle: never trust, always verify. IAM is the engine that makes Zero Trust work in practice.
In a Zero Trust architecture, no user, device, or application is trusted by default - regardless of whether they are inside or outside the corporate network. Every access request must be authenticated, authorized, and continuously evaluated:
- Continuous verification: IAM re-validates identity and context at every access attempt, not just at login
- Least privilege access: IAM enforces granular permissions so users access only what they need, when they need it
- Session-level controls: PAM and access management enforce real-time session policies and can revoke access instantly
- Microsegmentation support: IAM policies limit lateral movement by scoping access to specific network segments
Organizations implementing Zero Trust should treat IAM as the foundation - not an afterthought.
IAM Technologies and Tools
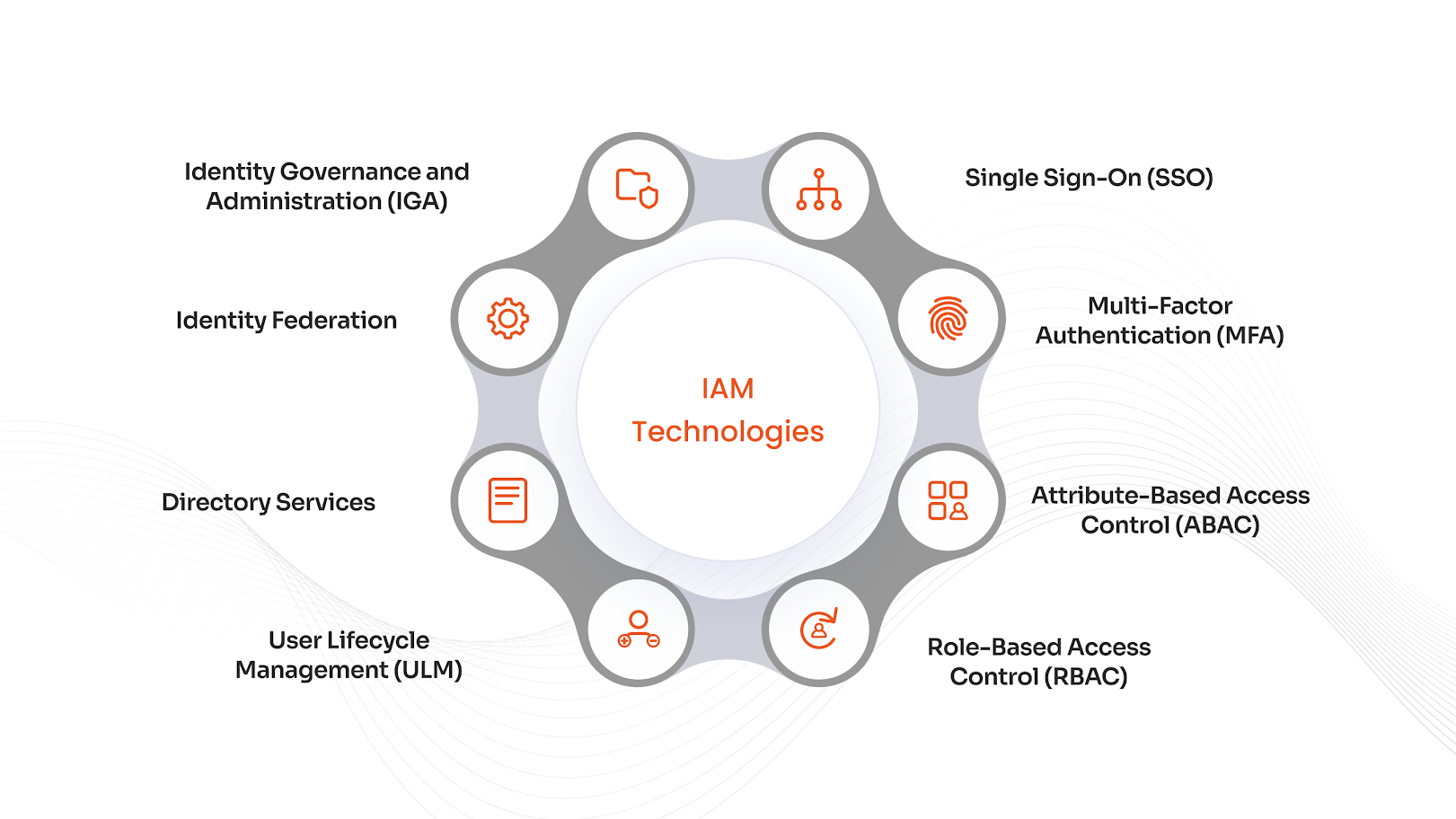
Single Sign-On (SSO)
SSO lets users authenticate once and access multiple applications without re-entering credentials. It reduces password fatigue, simplifies the login experience, and centralizes authentication management across all connected systems.
Multi-Factor Authentication (MFA)
MFA requires two or more independent verification factors - something you know (password), something you have (token), something you are (biometric). MFA dramatically reduces account takeover risk even when credentials are compromised.
Role-Based Access Control (RBAC)
RBAC assigns permissions based on predefined job roles. Separation of Duties (SoD) ensures no single user holds conflicting permissions that could enable fraud or error.
Attribute-Based Access Control (ABAC)
ABAC makes dynamic access decisions based on user attributes - department, location, device type, clearance level. It enables fine-grained, context-aware policy enforcement beyond static roles.
User Lifecycle Management
User lifecycle management automates account creation, role assignment, modification, and deprovisioning across the entire employee lifecycle, integrated with HR systems for real-time updates.
Identity Federation
Identity Federation enables users from different organizations or domains to access shared resources using their own credentials. It enables secure B2B and cross-domain collaboration without redundant credential management.
Identity Governance and Administration (IGA)
IGA provides oversight and automation for identity-related compliance processes: access reviews, role management, access certifications, and policy enforcement. Essential for organizations subject to SOX, HIPAA, or ISO 27001.
IAM Deployment Options
IAM solutions can be deployed in three primary models. The right choice depends on your infrastructure, compliance requirements, and IT capacity.
| On-Premise IAM | Cloud IAM (IDaaS) | Hybrid IAM | |
|---|---|---|---|
| Hosting | Your own infrastructure | Third-party cloud provider | Mix of both |
| Control | Full control over data and config | Managed by vendor | Balanced control |
| Maintenance | High IT overhead | Low - vendor managed | Medium overhead |
| Scalability | Limited by hardware | Elastic and instant | Flexible |
| Best for | Regulated industries with strict data residency needs | Remote-first or fast-scaling organizations | Organizations transitioning from legacy to cloud |
| What is Identity and Access Management as a Service (IDaaS)? IDaaS is cloud-delivered IAM. Instead of managing identity infrastructure on-premise, organizations subscribe to a cloud provider - like miniOrange - that delivers SSO, MFA, provisioning, and governance as a fully managed service. IDaaS reduces infrastructure costs, accelerates deployment, and scales effortlessly with organizational growth. |
|---|
IAM Protocols Explained
| Protocol | What It Does and When to Use It |
|---|---|
| SAML 2.0 | XML-based protocol for enterprise SSO. Enables identity providers (IdPs) to authenticate users and pass secure assertions to service providers (SPs). Best for corporate web application SSO. Widely adopted for its strong security and attribute-based access support. |
| OAuth 2.0 | Authorization framework that allows third-party applications to access user data without exposing credentials. Used for delegated access (e.g., Sign in with Google). Often paired with OpenID Connect for full authentication + authorization flows. |
| OpenID Connect (OIDC) | Authentication layer built on OAuth 2.0. Adds identity verification via JSON Web Tokens (JWT). Used for consumer-facing logins, social authentication, and modern web/mobile apps. Simpler and more scalable than SAML for most new deployments. |
| SCIM | Automates user provisioning and deprovisioning across cloud applications. Standardizes how identity data is exchanged between systems - critical for managing user lifecycles at scale across HR, IT, and SaaS platforms. |
| LDAP | Protocol for accessing and managing directory services (e.g., Active Directory). Foundational to on-premise IAM infrastructure for authentication, group management, and policy enforcement. Essential for legacy and hybrid environments. |
| RADIUS | Authentication protocol used primarily for network access control - VPNs, Wi-Fi, network switches. Common in hybrid IAM environments where legacy infrastructure must integrate with modern identity systems. |
Regulatory Compliance IAM Supports
A well-implemented IAM system is not just a security tool - it is a compliance infrastructure. Explore miniOrange's full compliance coverage to see how each regulation is addressed in detail.
| Regulation | How IAM Helps Achieve Compliance |
|---|---|
| GDPR | Enforces data minimization, consent management, and access restrictions for EU personal data. Supports privacy-by-design through role-based access and automated access reviews. miniorange.in/compliances/gdpr-compliance |
| HIPAA | Ensures only authorized personnel access protected health information (PHI). IAM enforces role-based access, MFA, and audit logging required under HIPAA's Security Rule. miniorange.in/compliances/hipaa-compliance |
| SOX | Enforces segregation of duties and monitors privileged access to financial systems. Maintains audit trails for financial reporting integrity. miniorange.in/compliances/sox-compliance |
| PCI DSS | Secures cardholder data through strong access controls, MFA enforcement, and user activity logging. Restricts access to payment systems. miniorange.in/compliances/pci-dss-compliance |
| ISO/IEC 27001 | Supports Annex A access control objectives, helping organizations demonstrate control over information assets and pass external audits. |
| FISMA / NIST CSF | Aligns with NIST identity and access control categories - supporting federal agencies in the identify, protect, detect, respond, and recover functions. |
| NIST SP 800-63 | The definitive US standard for digital identity. IAM systems built to this standard meet the strictest assurance levels for authentication and identity proofing. |
Benefits of Identity and Access Management
1. Significantly reduces breach risk
IAM eliminates weak, shared, or reused passwords through MFA, SSO, and passwordless authentication. By enforcing least privilege, it also limits the blast radius when credentials are compromised.
2. Enables regulatory compliance
Centralized auditing, access reviews, and policy enforcement give compliance teams the evidence they need for GDPR, HIPAA, SOX, PCI DSS, and more - without manual effort.
3. Streamlines user experience
SSO and automated lifecycle management mean employees spend less time on password resets and login friction, and IT spends less time on access requests. Productivity improves measurably.
4. Eliminates insider threats and access creep
IAM enforces least privilege and automates access revocation when roles change or users leave - preventing the accumulation of unnecessary permissions that insiders can exploit.
5. Supports Zero Trust architecture
IAM is the foundation of Zero Trust. Every access request is verified continuously, and granular session controls mean no implicit trust is ever granted based on network location alone.
6. Scales with your organization
Modern cloud IAM scales elastically - from 50 users to 500,000 - without requiring proportional IT investment. It adapts to remote workforces, M&A activity, and new cloud applications without disruption.
Choosing the Right IAM Solution
1. Assess your identity landscape
Map out the types of identities you need to manage: employees, contractors, customers, machines, APIs. The complexity of this landscape determines which IAM capabilities are non-negotiable.
2. Define deployment requirements
If your industry has strict data residency requirements (healthcare, government, financial services), on-premise or private cloud IAM may be necessary. For most organizations, cloud IAM (IDaaS) offers the fastest deployment, lowest TCO, and best scalability.
3. Verify protocol and integration support
Ensure the IAM product supports SAML, OAuth 2.0, OIDC, and SCIM for modern app integration - plus LDAP and RADIUS for legacy systems. miniOrange offers extensive app integrations covering Microsoft 365, Google Workspace, Salesforce, Workday, and thousands more.
4. Prioritize security and compliance capabilities
Must-have features: MFA with adaptive authentication, RBAC/ABAC, audit logging, access certifications, and privileged access controls. Verify compliance certifications relevant to your industry requirements.
5. Evaluate total cost and vendor support
Look beyond license pricing. Factor in implementation effort, training, ongoing maintenance, and support quality. A vendor with strong documentation and responsive support significantly reduces long-term costs.
miniOrange IAM: Simplified Identity and Access Management
miniOrange IAM is a comprehensive identity and access management platform built for organizations of all sizes. Trusted by 30,000+ organizations across 150+ countries.
What miniOrange IAM includes
- Single Sign-On (SSO): One login for all apps - 5,000+ pre-built connectors.
- Multi-Factor Authentication (MFA): 15+ authentication methods including biometrics and hardware tokens.
- Customer IAM (CIAM): Scalable identity management for end users and customers.
- Privileged Access Management (PAM): Secure and audit high-risk admin accounts.
- User Lifecycle Management: Automated provisioning integrated with HR systems.
- Legacy app support: Connects modern IAM to older LDAP, RADIUS, and on-premise systems.
IAM Best Practices
Enforce least privilege access
Grant users only the access required for their current role. Conduct quarterly access reviews and automate role adjustments triggered by HR changes. See least privilege best practices.
Make MFA mandatory - everywhere
MFA should be non-negotiable for all user accounts. Adaptive MFA scales authentication strength based on risk signals. Explore miniOrange MFA methods.
Automate user lifecycle management
Integrate IAM with your HR system so access is provisioned on day one, adjusted when roles change, and fully revoked the moment someone leaves. Learn about user lifecycle management.
Implement SSO to centralize access control
SSO reduces the attack surface (fewer credentials to steal), simplifies compliance auditing, and improves the employee experience. Explore miniOrange SSO.
Conduct regular access certifications
Periodic, automated access reviews keep permissions aligned with current job functions and provide the evidence required by most compliance frameworks. Assign accountability to data owners - not just IT.
Build toward Zero Trust from day one
Design your IAM policies assuming the network is already compromised. Enforce continuous verification, session-level controls, and microsegmentation from the start - retrofitting Zero Trust later is significantly harder.
Conclusion
Identity and Access Management is the foundation of every organization's security posture, compliance program, and digital operations. As workforces become more distributed, cloud adoption accelerates, and machine identities multiply, the IAM system you choose today will determine how resilient your organization is tomorrow.
Whether you are just beginning your IAM journey or modernizing a legacy deployment, miniOrange IAM provides the platform, integrations, and compliance coverage to move forward with confidence. Trusted by 30,000+ organizations worldwide.
Frequently Asked Questions
What is IAM (Identity and Access Management)?
IAM is a security framework that manages digital identities and controls who can access which systems, applications, and data within an organization. Learn more on the miniOrange IAM product page.
What is the difference between IAM and PAM?
IAM manages all user identities and access across an organization. PAM is a subset of IAM focused on high-privilege accounts that carry elevated security risk and require stricter controls.
What are the main components of an IAM system?
Key components include: authentication, authorization, SSO, MFA, user lifecycle management (provisioning/deprovisioning), RBAC, and identity governance (IGA).
What is Identity and Access Management as a Service (IDaaS)?
IDaaS is cloud-delivered IAM. Organizations subscribe to a provider - like miniOrange - that manages identity verification, SSO, MFA, and provisioning as a fully hosted service. Explore miniOrange cloud IAM.
How does IAM support Zero Trust security?
IAM is the foundation of Zero Trust. It enforces continuous identity verification, least-privilege access, and session-level authorization controls so no user or device is trusted by default, regardless of network location.
What is the difference between on-premise and cloud IAM deployment?
On-premise IAM is hosted within your own infrastructure - full control, higher maintenance cost. Cloud IAM (IDaaS) offers faster deployment, elastic scalability, and lower TCO. Hybrid IAM combines both, ideal for organizations transitioning from legacy to cloud.
What is miniOrange IAM?
miniOrange IAM is a comprehensive IAM platform offering SSO, MFA, CIAM, PAM, and user lifecycle management. It meets compliance requirements including GDPR, HIPAA, and SOX. Trusted by 30,000+ organizations across 150+ countries.
What is an IAM product?
An IAM product is a software platform implementing authentication, authorization, SSO, MFA, provisioning, governance, and audit logging for an organization. miniOrange IAM is purpose-built for enterprises of all sizes.
Leave a Comment