For years, Privileged Access Management (PAM) was built around a simple assumption: privileged access is primarily a human problem. That assumption is rapidly collapsing.
Modern enterprises are no longer driven mainly by administrators logging into servers. They are increasingly powered by APIs, containers, automation pipelines, microservices, cloud workloads, and AI-driven systems communicating continuously at machine speed. In many organizations today, machine identities already outnumber human identities by massive margins — and every one of those systems requires identity.
Service accounts, API tokens, Kubernetes workloads, cloud functions, workload certificates, and automation bots are becoming the operational backbone of the enterprise. Yet many organizations are still trying to secure this new environment using PAM architectures originally designed for interactive human sessions. That mismatch is becoming one of the most important architectural problems in enterprise security today.
This is no longer simply a PAM challenge. It is a trust architecture challenge.
Traditional PAM Was Designed for a Human-Centric Enterprise
Traditional PAM systems emerged in an era of relatively stable infrastructure. The security model was straightforward: store privileged credentials in centralized vaults, tightly control administrator access, rotate passwords periodically, and monitor privileged sessions for audit and compliance purposes.
That architecture worked well because the enterprise itself was predictable. Infrastructure was persistent, identities were mostly human, and privileged access was relatively infrequent and interactive.
Modern environments operate very differently. Applications now scale dynamically across cloud platforms. Containers are instantiated and destroyed continuously. CI/CD pipelines provision infrastructure automatically. APIs communicate autonomously across distributed systems. AI agents increasingly interact directly with production environments. The enterprise is evolving into a highly dynamic identity ecosystem — and that fundamentally changes how trust must be established.
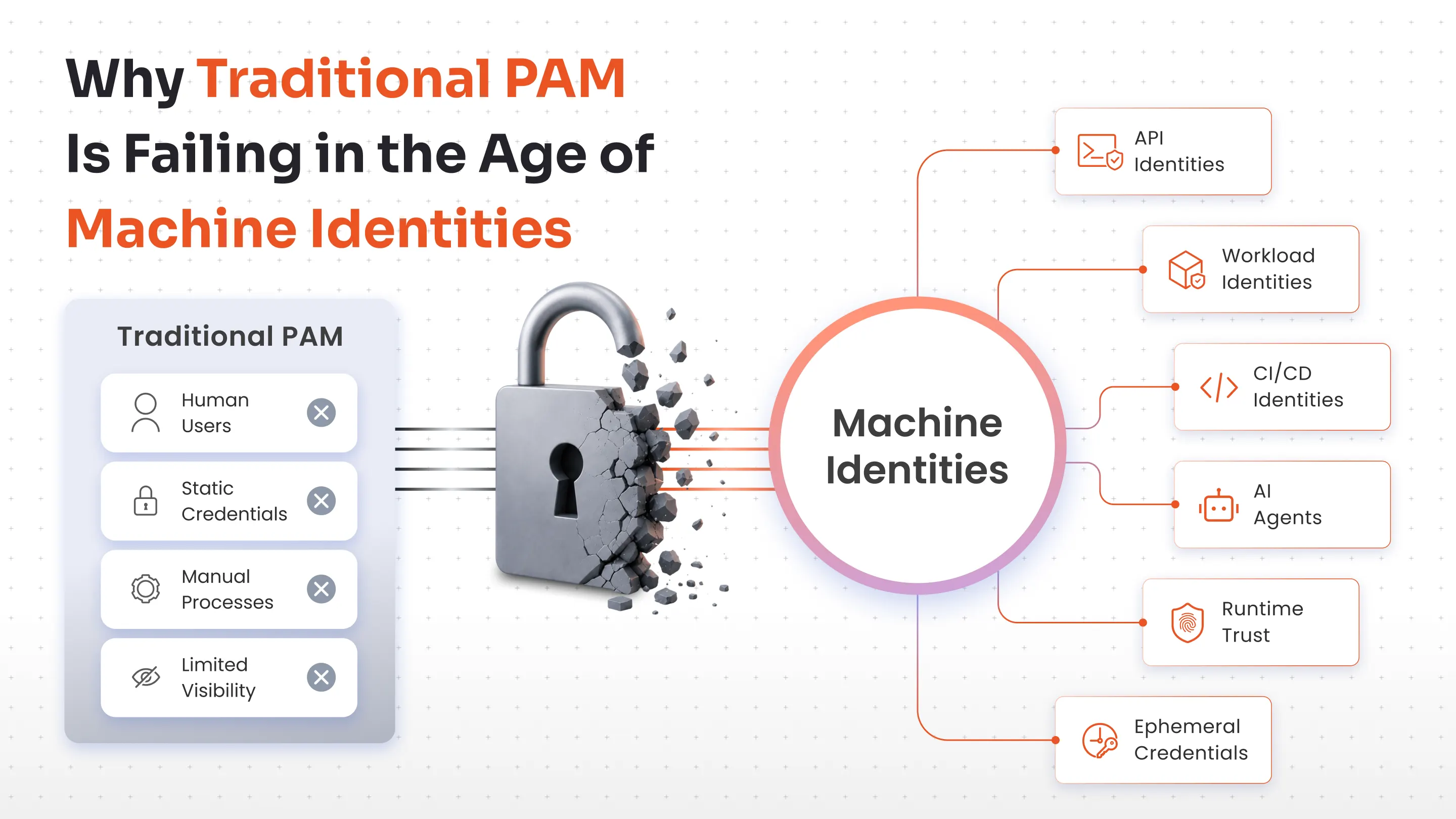
Why Traditional PAM Models Are Starting to Break
One of the biggest weaknesses in traditional PAM architectures is their dependence on centralized credential vaulting. In cloud-native environments where workloads scale continuously and identities may exist only briefly, vault-centric models begin creating operational strain. Thousands of workloads requesting secrets simultaneously introduce latency, scalability concerns, and architectural fragility.
More importantly, static credential distribution fundamentally conflicts with ephemeral infrastructure. A container that exists for a few minutes should not depend on a long-lived shared credential that may persist for months.
At the same time, organizations continue relying heavily on API keys, service account passwords, embedded secrets, and long-lived certificates. Over time, those secrets become scattered across CI/CD pipelines, repositories, infrastructure templates, configuration systems, and automation scripts. Secrets sprawl quickly becomes difficult to inventory, govern, and rotate effectively. The problem is no longer simply securing credentials — it is reducing dependency on persistent credentials altogether.
The Scale Problem
Traditional PAM workflows assume human involvement: a user requests access, someone approves it, a session begins, and activity is reviewed later. That model becomes impractical when machine-to-machine authorization decisions occur millions of times per hour. Modern systems require trust evaluation that is continuous, automated, contextual, and runtime-aware.
The Session Problem
Legacy PAM platforms were designed around SSH sessions, RDP sessions, and human command execution. But modern workloads interact primarily through APIs, service meshes, tokens, and workload identities. In many cases, there is no interactive session to monitor anymore. Instead, security teams must evaluate runtime behavior itself — service-to-service trust, token issuance patterns, workload behavior, east-west traffic anomalies, and identity propagation across distributed environments. The control plane is shifting from session management to runtime authorization.
Machine Identities Are Becoming the New Enterprise Perimeter
The rise of machine identities is fundamentally reshaping enterprise security architecture. In many ways, machine identities are becoming the new perimeter. The ability to continuously validate trust between workloads, services, APIs, automation systems, and AI agents may soon become more important than traditional network boundaries themselves.
As a result, security architectures are beginning to shift away from static credential management and toward dynamic identity validation. Organizations are increasingly adopting:
- Short-lived credentials instead of persistent, long-lived secrets
- Federated workload identities instead of shared credential pools
- Continuous authorization models instead of standing privilege grants
- Runtime-aware trust evaluation instead of periodic access reviews
This represents a much deeper architectural transition than simply modernizing PAM tooling. Identity itself is evolving into operational infrastructure embedded directly into runtime systems.
Security architectures are beginning to shift from static credential management toward dynamic identity validation — a transition far deeper than simply modernizing PAM tooling.
The AI Layer: How PAM Must Evolve
Machine identity ecosystems generate enormous volumes of telemetry and continuously changing trust relationships. Traditional rule-based PAM models cannot adapt fast enough to evaluate risk dynamically at this scale. This is where AI becomes transformative.
The role of AI in future PAM systems is not simply improving dashboards or generating better alerts. The deeper shift is architectural — AI increasingly becomes part of the runtime trust decision itself.
From Binary to Contextual Trust
Traditional PAM systems largely ask a binary question: does this identity possess valid credentials? Future PAM systems increasingly ask a more contextual question: should this identity be trusted right now under current conditions? That trust evaluation may include behavioral patterns, runtime context, communication history, workload integrity, environmental signals, and risk posture — shifting security from credential validation toward trust computation.
Continuous Privilege Evaluation
Traditional PAM systems typically grant access until it is manually revoked or periodically reviewed. But machine identities are highly dynamic — workloads scale continuously, privilege requirements change rapidly, and trust relationships evolve in real time. As a result, privilege itself must become continuously evaluated rather than statically assigned.
AI-assisted systems can establish behavioral baselines for workloads and machine identities, learning which services normally communicate with each other, how APIs typically behave, and what normal workload execution patterns look like. When behavior deviates significantly from those baselines, systems can dynamically increase scrutiny, reduce privileges, or trigger adaptive authorization controls automatically. This enables earlier detection of:
- Compromised workloads and credential abuse
- Abnormal privilege escalation attempts
- Lateral movement across distributed systems
- Rogue automation behavior and anomalous API activity
Evolving Human Roles
At machine scale, humans cannot review every authorization decision manually. Instead, security teams increasingly define trust boundaries, governance guardrails, and acceptable risk policies while AI-driven systems evaluate runtime risk dynamically within those boundaries. The focus shifts from operational approvals to trust orchestration. Human roles evolve from reactive reviewers to architects of the governance framework itself.
The Future of PAM
PAM platforms are evolving from vault-centric systems into runtime trust orchestration platforms. The future architecture will likely combine:
- Continuous telemetry analysis across cloud-native infrastructure
- Federated workload identity with cryptographic attestation
- AI-assisted behavioral modeling and anomaly detection
- Dynamic privilege recalculation based on runtime context
- Runtime authorization engines integrated directly into application layers
- Event-driven policy enforcement that adapts to changing conditions
In this world, trust is no longer static. It becomes adaptive, contextual, and continuously evaluated. And that evolution is necessary because machine identities are fundamentally changing the scale, speed, and complexity of enterprise trust relationships.
Closing Perspective
The enterprise security industry spent years optimizing how humans access systems. The next decade will be defined by how systems establish trust with other systems.
Machine identities are not simply extending traditional PAM models. They are forcing a redesign of enterprise trust architecture itself. The organizations that recognize this shift earliest — and act on it with deliberate architectural intent — will be best positioned to secure the autonomous, machine-driven environments that define the modern enterprise.
The future of PAM will not revolve solely around vaults and passwords. It will become runtime-aware, identity-centric, continuously adaptive, and deeply integrated into the operational fabric of the autonomous enterprise.

Leave a Comment