Perimeter-based security is gradually losing relevance. In modern environments, access decisions are driven by identity rather than network location. Identity security posture management focuses on continuously evaluating those identities, understanding their risk, and ensuring that access remains appropriate at all times.
Understanding Identity Security Posture Management
To better understand the identity security posture management definition, it helps to view it as an evolution of identity security rather than a standalone tool category.
Identity security posture management (ISPM) is a discipline that enables organizations to assess, monitor, and improve the security state of identities across systems, applications, and infrastructure.
Unlike traditional identity solutions that concentrate on provisioning or authentication, ISPM - identity security posture management operates continuously. It analyzes how identities behave, what access they accumulate, and whether that access aligns with security policies. This ongoing evaluation allows teams to detect risk conditions that static controls typically miss.
At a strategic level, identity security posture management provides three core outcomes:
- continuous visibility into identity exposure across environments
- contextual risk analysis based on access patterns and configurations
- automated enforcement mechanisms to reduce excessive or unnecessary access
This makes ISPM less about managing identities and more about managing identity risk at scale.
Why Identity Posture Management Is Critical in 2026
Identity-related threats are no longer edge cases. They represent a dominant attack vector. According to industry reports, 2026 has already seen a massive uptick in data breaches, with 69% organizations citing inadequate identity security capabilities as the reason.
Credential compromise, phishing-led access, and misuse of privileged accounts continue to appear in a significant portion of reported breaches.
Several structural shifts explain this trend:
Credential-Based Attacks Attackers prioritize credentials because they provide legitimate access pathways. Once obtained, they allow lateral movement without triggering traditional perimeter defenses.
Identity Sprawl Organizations now operate across SaaS platforms, cloud providers, and internal systems. Each environment introduces new identities, roles, and access relationships. Over time, this creates a fragmented and difficult-to-govern identity landscape.
Configuration Drift Permissions change frequently. Users switch roles, projects evolve, and systems integrate with new tools. Without continuous validation, access rights quickly diverge from intended policies.
The limitation of many existing approaches is their reliance on periodic review cycles. Quarterly certifications or manual audits cannot keep pace with real-time changes. This gap is exactly where identity security posture management (ISPM) becomes relevant.
With a posture-driven approach, organizations can:
- Detect risky permissions before they are exploited
- Maintain consistent enforcement of access policies
- Identify anomalies in authentication and authorization behavior
- Align identity controls with Zero Trust principles through continuous validation
How Identity Security Posture Management Works
ISPM follows a lifecycle model that focuses on continuous improvement rather than one-time configuration.
1. Discover: The first step is building a complete inventory of identities. This includes employees, partners, contractors, service accounts, APIs, and workloads. Without this baseline, risk analysis remains incomplete.
2. Assess Each identity is evaluated based on its access level, privilege relationships, authentication methods, and behavioral patterns. Risk scoring models help prioritize which identities require immediate attention.
3. Monitor Ongoing monitoring ensures that changes in access, configuration, or behavior are detected as they occur. This is essential for identifying privilege escalation, dormant accounts, or policy violations.
4. Remediate Once risks are identified, remediation workflows adjust permissions, enforce policies, or trigger alerts. Automation plays a critical role here to reduce response time and operational overhead.
Key Components of Identity Security Posture Management
A functional identity security posture management program is built on a set of tightly connected capabilities that move beyond static identity controls. Each component contributes to continuous visibility, risk evaluation, and access correction.
- Identity Discovery and Inventory
The starting point is full visibility. Organizations need a unified inventory of all identities across cloud platforms, SaaS applications, on-prem systems, and hybrid environments. This includes users, third-party collaborators, service accounts, APIs, and workloads. Without this baseline, risk analysis is incomplete because unknown identities cannot be secured or governed.
- Risk Assessment and Scoring
Not all identities carry the same level of risk. ISPM platforms evaluate identities based on privilege levels, access breadth, authentication strength, and behavioral signals. Context is critical here. An identity with moderate access but weak authentication may be riskier than a highly privileged account with strict controls. Risk scoring helps teams prioritize remediation efforts instead of treating all identities equally.
- Entitlement Management
Entitlements define what an identity can access and how. ISPM systems map these permissions in detail, including direct assignments, inherited group memberships, role-based access, and indirect privilege paths.
This analysis surfaces:
- excessive permissions that exceed job requirements
- unused access that can be removed safely
- conflicting privilege combinations that violate separation-of-duties principles
Least privilege enforcement is driven by comparing granted access with actual usage patterns. Permissions that are never used become immediate candidates for removal.
- MFA and Authentication Gap Detection
Authentication remains a primary control point, but coverage is often inconsistent. ISPM identifies identities that lack strong authentication mechanisms such as multi-factor authentication (MFA) or rely on weaker methods. These gaps are especially critical for privileged and externally exposed accounts, where a single compromised credential can lead to broader access.
- Continuous Posture Monitoring
Identity risk is not static. Access changes, roles evolve, and new integrations introduce additional exposure. Continuous monitoring tracks these changes in real time, identifying anomalies such as privilege escalation, dormant accounts being reactivated, or deviations from expected access patterns. This ensures that risk is detected as it emerges rather than during scheduled reviews.
- Automated Remediation Workflows
Detection without action creates operational bottlenecks. ISPM platforms integrate remediation workflow automation that adjusts permissions, enforces policies, or triggers approval processes. This reduces manual intervention and shortens the time between risk identification and resolution.
- Compliance Reporting and Audit Readiness
Identity data must be translated into evidence that aligns with regulatory frameworks. ISPM systems maintain detailed audit trails of access decisions, policy enforcement, and remediation actions. They also generate structured reports mapped to standards such as SOC 2, ISO 27001, PCI DSS, HIPAA, and GDPR. This shifts compliance from a periodic activity to a continuous process.
- Non-Human Identity Governance
A significant portion of modern environments consists of identities that are not tied to individual users. These include service accounts, machine identities, containers, and application workloads.
Effective governance in this area involves:
- tracking lifecycle events such as provisioning and deprovisioning
- restricting permissions to only what is operationally required
- monitoring for excessive or unused access
- enforcing strict access controls and credential management
These non-human identities often operate with elevated privileges and limited oversight, which makes them a high-value target if left unmanaged.
Together, these components define how identity security posture management operates in practice. When comparing identity security posture management vendors, it is advisable look for solutions that demonstrate these capabilities.
ISPM vs. IAM vs. IGA vs. PAM: What's the Difference?
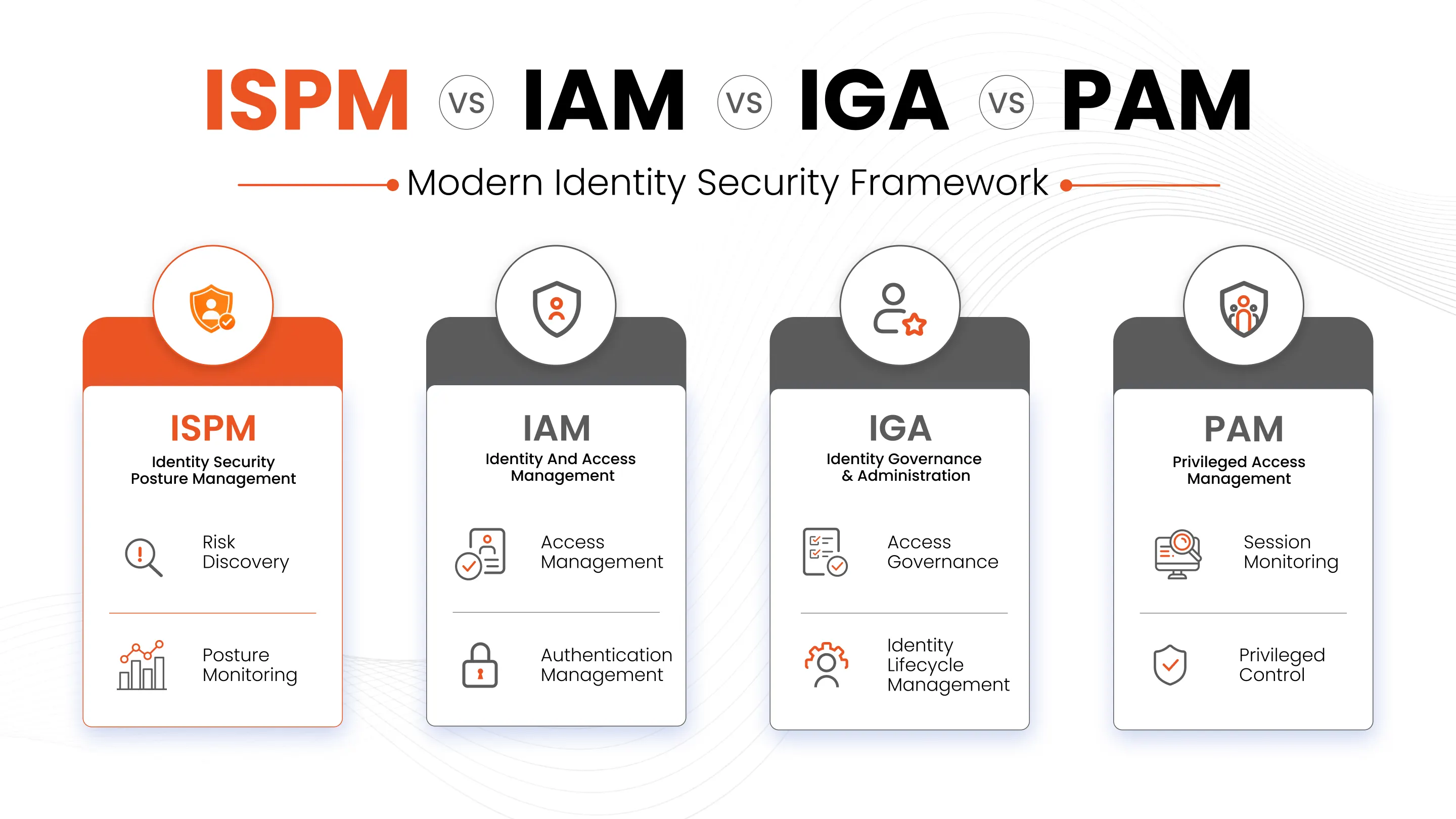
These terms are often grouped together, but they solve different problems. Treating them as interchangeable leads to gaps in coverage, especially when it comes to continuous risk evaluation.
ISPM vs. IAM
Identity and Access Management (IAM) is responsible for the operational side of identity. It handles account creation, authentication, password policies, and access enforcement at login. IAM solutions answer questions like: can this user log in, and what resources are they allowed to access?
Identity security posture management, on the other hand, evaluates whether those access decisions are actually safe over time. In practical terms, IAM establishes access. ISPM continuously audits and challenges it.
ISPM vs. IGA
Identity Governance and Administration (IGA) focuses on oversight and control processes. It manages access requests, approval workflows, role definitions, and periodic certification campaigns. IGA answers structured governance questions such as: who approved this access, and has it been reviewed?
ISPM - identity security posture management extends beyond governance by introducing continuous, real-time evaluation of identity risk.
A useful way to frame it: IGA confirms that access was approved. ISPM determines whether that approval still makes sense from a security standpoint.
ISPM vs. PAM
Privileged Access Management (PAM) solution is designed to secure high-risk accounts that have elevated permissions. It focuses on controlling how privileged credentials are stored, accessed, and used. Typical PAM capabilities include credential vaulting, session monitoring, just-in-time access, and approval workflows for sensitive actions.
Identity security posture management, in contrast, evaluates whether privileged access is appropriate in the first place and whether it remains justified over time.
From a workflow perspective, PAM solutions act as a control layer around privileged activity. ISPM acts as an analytical layer that identifies where privilege is over-assigned, misconfigured, or no longer required.
ISPM and Regulatory Compliance
Compliance is one of the clearest business cases for ISPM. A strong posture management program creates the evidence trail auditors want, including access reviews, remediation actions, policy violations, and identity lifecycle history.
ISPM capabilities are built to reduce manual effort, supporting audit readiness, and help maintain continuous compliance. This matters across frameworks such as SOC 2, ISO 27001, PCI DSS, HIPAA, GDPR, and NIST-oriented control environments.
When comparing identity security posture management vendors, look for continuous discovery, real-time risk scoring, entitlement analysis, non-human identity coverage, and workflow automation. Those are the capabilities that turn identity data into usable compliance evidence.
Frequently Asked Questions
What is the simplest way to define identity security posture management?
The simplest identity security posture management definition is this: a continuous process for discovering identities, measuring identity risk, monitoring access posture, and remediating exposure across the enterprise.
Why is ISPM gaining traction now?
The increase in cloud adoption, SaaS usage, and identity-based attacks has made traditional identity controls insufficient. Continuous posture management addresses these gaps directly.
Is ISPM a replacement for IAM or PAM?
No. ISPM works alongside IAM, IGA, and PAM. It enhances these systems by adding continuous risk evaluation and posture visibility.
How should teams evaluate identity security posture management vendors?
Focus on depth of identity discovery, quality of risk scoring, support for least privilege, automation for remediation, and evidence generation for compliance. Those capabilities separate posture management from basic identity administration.

Leave a Comment