In a world where data breaches cost organisations an average of $4.88 million per incident (IBM, 2024), knowing who can access what inside your organisation is no longer optional. Identity and Access Management (IAM) is the security framework that answers this question at scale.
But IAM is not a single product or a single policy. It rests on four foundational pillars: Access Management, Privileged Access Management, Active Directory Management, and Identity Governance and Administration. Each pillar addresses a distinct layer of your organisation's security posture.
In this guide, we break down each of the four pillars of IAM, explain what they do, why they matter, and how miniOrange's Unified Identity Platform brings them together into one coherent, enterprise-ready solution.
What Is IAM and Why Does It Matter?
Identity and Access Management (IAM) is a framework of policies, processes, and technologies designed to ensure that the right people have access to the right resources at the right time, and for the right reasons. It governs every digital identity inside your organisation, from full-time employees to contractors, APIs, and automated systems.
IAM sits at the intersection of security, compliance, and productivity. Done well, it reduces the attack surface, enables regulatory compliance (GDPR, HIPAA, SOC 2), and removes friction from everyday user workflows.
Effective IAM is the backbone of a Zero Trust security model, which operates on the principle of 'never trust, always verify.' Rather than assuming users inside the network are safe, Zero Trust requires continuous verification of every identity, device, and session.
As hybrid work, cloud adoption, and third-party integrations have expanded the digital perimeter, IAM has become one of the most critical investments an organisation can make. The four pillars below are the building blocks of that investment.
The Four Pillars of IAM Explained
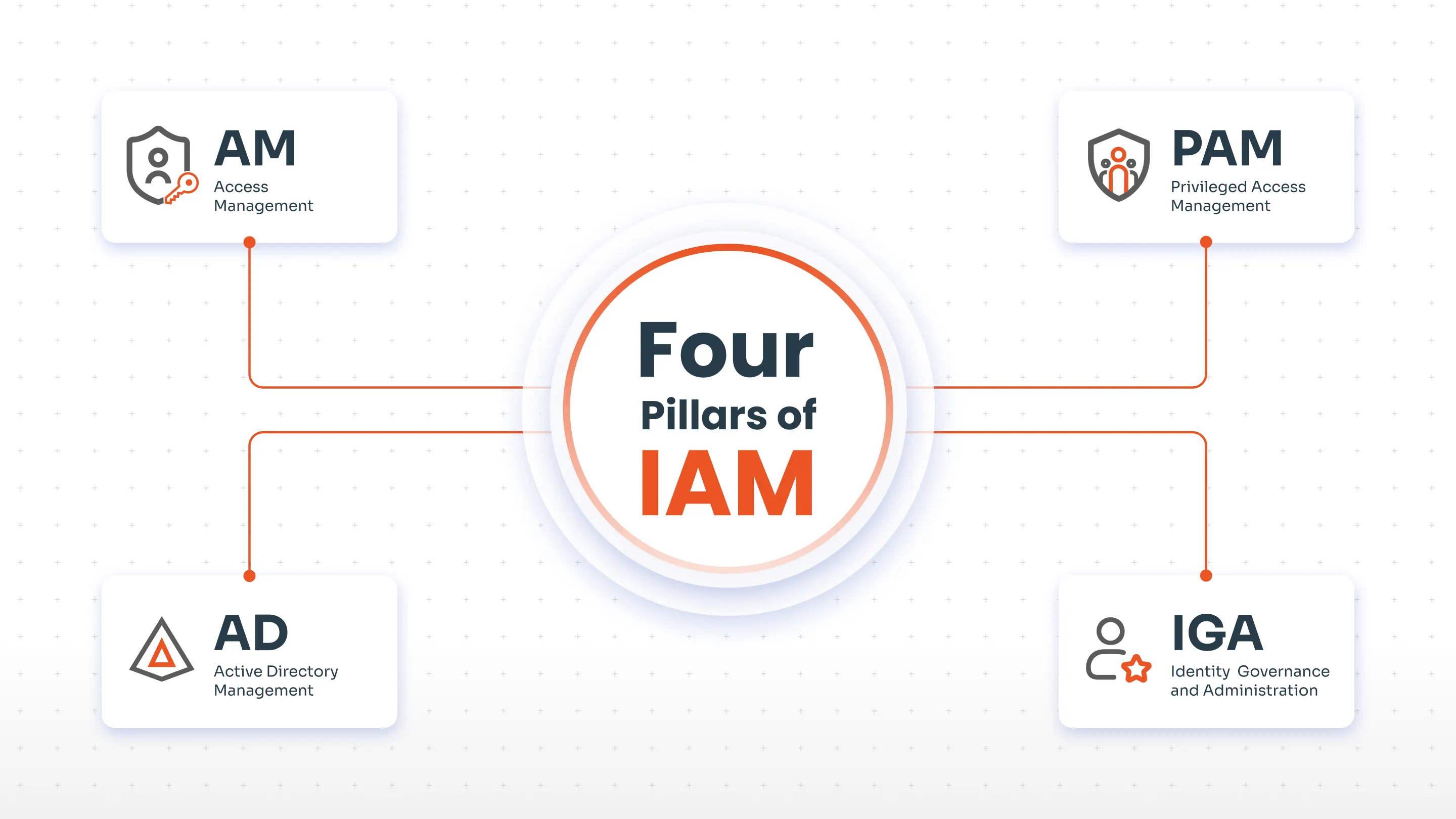
IAM is most commonly anchored by four core components:
- Access Management (AM): Controls who can access which resources and under what conditions.
- Privileged Access Management (PAM): Secures high-risk accounts with elevated permissions.
- Active Directory Management (AD Management): Manages identities and access within Microsoft Active Directory environments.
- Identity Governance and Administration (IGA): Provides oversight, compliance, and lifecycle management across all identities.
Each pillar is distinct, but they work together. A mature IAM programme integrates all four to create a layered, resilient security posture.
Pillar 1: Access Management (AM)
What Is Access Management?
Access Management (AM) is the core IAM pillar responsible for controlling how and when users can access resources, whether those resources are internal applications, cloud services, or sensitive data repositories. It is the gatekeeper that enforces your organisation's access policies in real time.
Key Features of Access Management
- Centralised role and permission management: Administrators define and manage all user roles from a single, unified platform, simplifying the process of assigning and adjusting permissions as user roles evolve.
- Role-Based Access Control (RBAC): Access is restricted based on the user's role, ensuring employees only reach the resources relevant to their job functions. This is a core principle of the least privilege model.
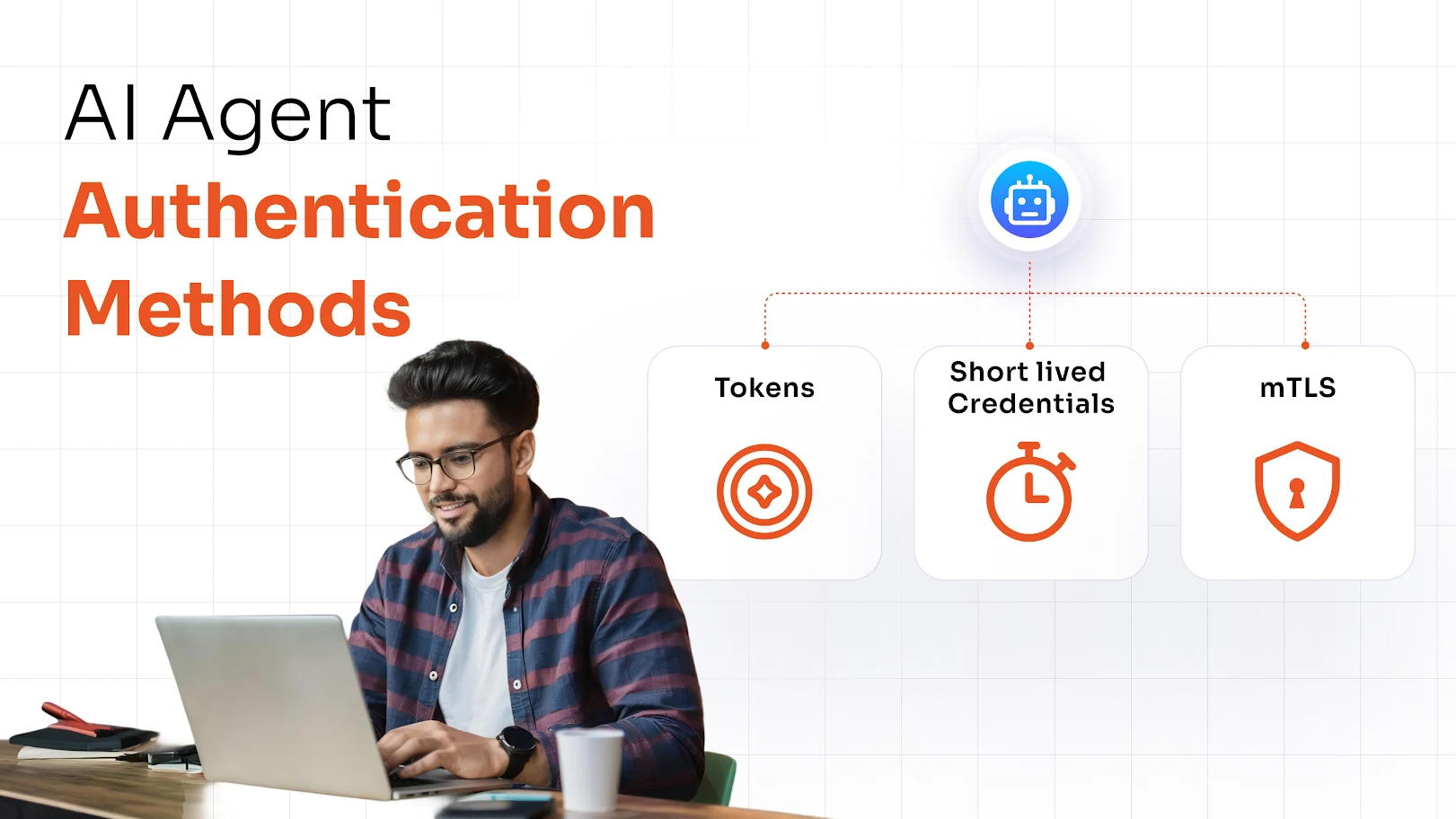
- Multi-Factor Authentication (MFA): Users must provide two or more verification factors before gaining access, significantly reducing the risk of credential-based attacks.
- Support for multiple authentication protocols: AM systems support SAML, OAuth 2.0, OpenID Connect, and LDAP, enabling secure access across diverse environments and applications.
- Temporary privilege assignment: Elevated access can be granted for a defined time window, ensuring that higher-level permissions are not left active indefinitely.
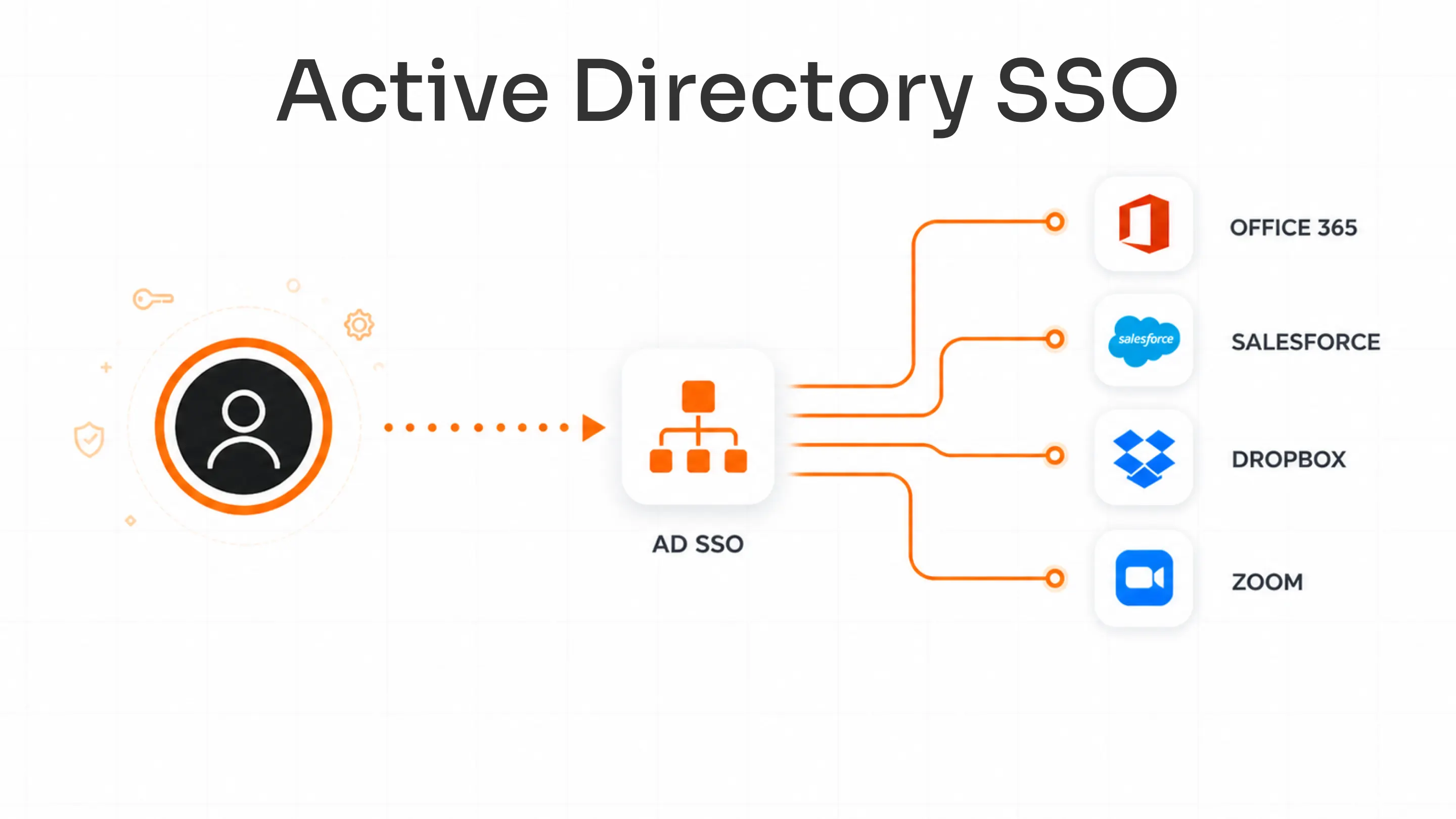
- Single Sign-On (SSO): Users authenticate once and gain access to all authorised applications, reducing password fatigue and improving productivity.
Why AM Matters
Without Access Management, organisations resort to siloed, manual permission management, a process that is slow, error-prone, and impossible to audit at scale. AM ensures that access decisions are consistent, policy-driven, and revocable the moment a user's role changes.
Pillar 2: Privileged Access Management (PAM)
What Is Privileged Access Management?
Privileged Access Management (PAM) is a specialised IAM pillar that focuses on securing accounts with elevated permissions, such as system administrators, database owners, DevOps engineers, and service accounts. These accounts are high-value targets for attackers; compromising a single privileged account can give an adversary unrestricted access to critical infrastructure.
PAM enforces the principle of least privilege at the highest-risk level of your organisation, ensuring that even trusted insiders cannot misuse their access.
Key Features of PAM
- Centralised management of privileged accounts and credentials: All privileged access is controlled and monitored from one platform, preventing shadow admin accounts and untracked credentials.
- Fine-grained permissions: Organisations assign the minimum level of access necessary for each privileged role, significantly reducing the attack surface.
- Customised approval workflows: Privileged actions require explicit authorisation before execution, adding a critical layer of oversight.
- Automated password rotation: Privileged account passwords are rotated automatically on a defined schedule, minimising the window of exposure for any compromised credential.
- Session monitoring and auditing: All privileged sessions are recorded and analysed, enabling real-time oversight and providing a detailed audit trail for compliance and forensic investigations.
- Just-in-Time (JIT) access: Elevated access is granted only when needed and automatically revoked upon task completion, eliminating standing privileges.
Why PAM Matters
Verizon's 2024 Data Breach Investigations Report found that over 74% of breaches involved a human element, with privileged account misuse among the leading causes. PAM directly addresses this risk by ensuring that even the most powerful accounts inside your organisation are tightly governed. See how miniOrange PAM protects privileged accounts.
Pillar 3: Active Directory Management (AD Management)
What Is Active Directory Management?
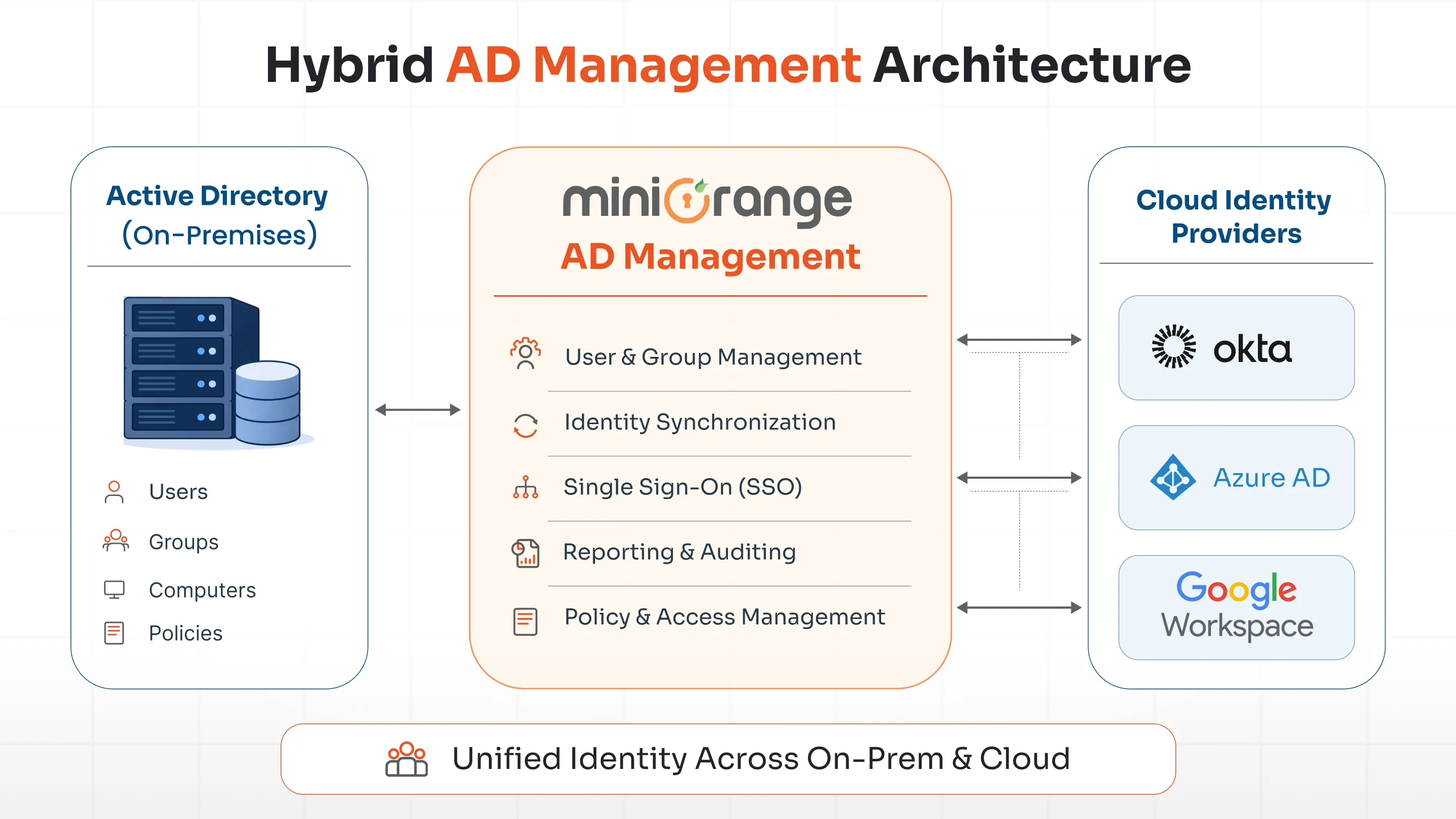
Active Directory Management (AD Management) focuses on governing identities and access within Microsoft Active Directory (AD) environments. For most enterprises, Active Directory is the authoritative source for user identities, group memberships, and access policies across on-premises systems. As organisations extend to the cloud, managing AD effectively becomes both more complex and more critical.
Key Features of AD Management
- Seamless integration with cloud identity providers: AD Management bridges on-premises AD with cloud directories such as Azure AD, Okta, and Google Workspace, enabling unified identity management across hybrid environments.
- Automated provisioning and de-provisioning: User accounts, group memberships, and access rights are created, updated, and revoked automatically based on defined lifecycle events (joining, role changes, departures).
- Robust monitoring, auditing, and reporting: All changes within Active Directory are logged and reportable, providing visibility into user activities and supporting compliance requirements.
- Role-Based Access Control (RBAC) enforcement: AD Management ensures that group memberships and access policies are aligned with organisational roles, reducing over-privileged accounts.
- Protection against AD misconfigurations: Common Active Directory vulnerabilities, including Kerberoasting, pass-the-hash, and excessive group memberships, are detected and remediated.
Why AD Management Matters
Despite the cloud shift, Active Directory remains the identity backbone for the majority of enterprise organisations. Misconfigurations and unmonitored changes in AD are among the most exploited attack vectors in modern ransomware and lateral movement campaigns. Effective AD Management prevents attackers from exploiting these gaps while ensuring that identity data stays accurate and consistent across your entire environment.
Pillar 4: Identity Governance and Administration (IGA)
What Is Identity Governance and Administration?
Identity Governance and Administration (IGA) is the IAM pillar that provides strategic oversight and policy enforcement across all digital identities in an organisation. While AM, PAM, and AD Management are operational, IGA is the governance layer: it defines the rules, conducts the reviews, enforces the policies, and produces the audit evidence that regulators require.
Key Features of IGA
- Automated access request and approval workflows: Users can request access through a self-service portal, with requests automatically routed to the appropriate approvers based on predefined policies.
- Automated provisioning and de-provisioning: IGA systems automatically grant or revoke access as users join, change roles, or leave the organisation, eliminating the risk of orphaned accounts and excessive permissions.
- Entitlement management: IGA defines and enforces what resources users can access based on their roles, attributes, and organisational policies.
- Segregation of Duties (SoD) enforcement: IGA prevents individuals from holding conflicting access rights that could enable fraud or errors, a requirement for SOX, PCI-DSS, and other frameworks.
- Access review and certification campaigns: Periodic access reviews ensure that existing permissions remain appropriate. Managers can certify or revoke access through intuitive review workflows.
- Analytics and reporting: IGA platforms provide deep visibility into who has access to what, enabling informed decision-making and producing audit-ready compliance reports.
Why IGA Matters
IGA is what transforms IAM from a security tool into a governance programme. Without IGA, organisations accumulate access risk over time as roles change and permissions drift. With IGA, access is continuously right-sized, auditable, and compliant. For organisations subject to GDPR, HIPAA, ISO 27001, or SOC 2, IGA is not optional.
Key Aspects to Evaluate in an IAM Solution
When selecting an IAM platform, four operational dimensions determine day-to-day effectiveness:
| Aspect | What to Look For |
|---|---|
| User Management | Comprehensive tracking of all users, their roles, permissions, and access rights. The platform should handle the full identity lifecycle from onboarding to offboarding. |
| Authentication and Authorisation | Strong support for MFA, SSO, and modern protocols (SAML, OAuth, OIDC). Adaptive authentication that adjusts requirements based on risk context is a major advantage. |
| Access Reviews | Automated, scheduled access certification campaigns that allow managers to review and certify or revoke access. Essential for SOX, PCI-DSS, and ISO 27001 compliance. |
| Onboarding and Offboarding | Automated provisioning ensures new users get the right access from day one. Automated de-provisioning ensures that departing users lose all access immediately, eliminating the risk of orphaned accounts. |
Summary
- IAM is a framework that ensures the right people have the right access to the right resources at the right time.
- Access Management (AM) is the operational layer that enforces access policies through RBAC, MFA, and SSO.
- Privileged Access Management (PAM) secures your highest-risk accounts through granular controls, session monitoring, and JIT access.
- Active Directory Management bridges on-premises and cloud identity environments, automating provisioning and protecting against AD-specific attack vectors.
- Identity Governance and Administration (IGA) is the governance layer: it enforces policies, runs access reviews, and produces the compliance evidence regulators need.
- A unified IAM platform, like miniOrange's Unified Identity Platform, integrates all four pillars into one coherent, enterprise-ready solution.
Conclusion
The four pillars of IAM are not independent initiatives. They are complementary layers of a mature identity security strategy. Access Management handles everyday access decisions. PAM protects your most sensitive accounts. AD Management keeps your identity directory accurate and secure. And IGA provides the governance oversight that ties everything together.
miniOrange's Unified Identity Platform integrates all four pillars into a single, cloud-ready solution. Whether you are just starting your IAM journey or looking to consolidate a fragmented identity stack, miniOrange can help you build a comprehensive, scalable, and compliant IAM programme.
Frequently Asked Questions
What are the four pillars of IAM?
The four pillars of Identity and Access Management are: Access Management (AM), Privileged Access Management (PAM), Active Directory Management (AD Management), and Identity Governance and Administration (IGA). Together they cover access control, privileged account security, directory management, and governance across an organisation's entire identity landscape.
What is the difference between IAM and PAM?
IAM is the broader framework that manages all digital identities and their access rights. PAM (Privileged Access Management) is a specialised subset of IAM focused specifically on accounts with elevated permissions, such as system administrators, database owners, and service accounts. Think of IAM as the entire house, and PAM as the reinforced vault inside it.
Why is Identity Governance and Administration (IGA) important?
IGA ensures that access rights across your organisation remain accurate, appropriate, and auditable over time. Without IGA, organisations accumulate access risk as roles change and permissions drift. IGA enforces Segregation of Duties (SoD), runs access certification campaigns, and produces the compliance evidence required by GDPR, HIPAA, SOX, and ISO 27001.
How does IAM support Zero Trust security?
IAM is foundational to Zero Trust architecture. Zero Trust operates on the principle of 'never trust, always verify,' meaning every access request, regardless of whether it originates inside or outside the network, must be authenticated, authorised, and continuously validated. IAM provides the identity verification, policy enforcement, and audit capabilities that Zero Trust requires.
What is the least privilege principle in IAM?
The principle of least privilege states that users, applications, and systems should only have the minimum level of access required to perform their specific function, and nothing more. It is enforced through RBAC in Access Management, fine-grained permissions in PAM, and entitlement management in IGA. Least privilege significantly reduces the blast radius of any compromised account.
How does miniOrange help with IAM implementation?
miniOrange offers a Unified Identity Platform that integrates all four pillars of IAM into a single, cloud-ready solution. miniOrange supports on-premises, cloud, and hybrid environments, and provides dedicated implementation support, compliance reporting, and integrations with popular directories, applications, and protocols.

Leave a Comment