Managing JD Edwards user access by hand quickly becomes a hardship, especially as your team grows and roles shift constantly. You end up with deprovisioning that drags on for weeks, role assignments that don't match job descriptions, and audit trails scattered across emails and spreadsheets. These aren't one-off problems. They happen predictably when manual processes try to handle enterprise-scale demands in a fast-moving business environment.
That's where automated user provisioning for JD Edwards steps in. It brings policy-driven controls to every identity lifecycle event, from the moment someone joins to their final offboarding. In this post, we'll define it clearly, explain why it's a game-changer for modern ERP security, and dive into the five biggest benefits that make it a priority for any organization running JD Edwards in regulated industries.
Why Automated User Provisioning for JD Edwards Is Critical for Modern ERP Security
Growing risk in manual JD Edwards access management
Think about the typical flow in a mid-sized enterprise. HR flags a new hire or departure in their system, but IT gets swamped with tickets from a backlog of 200+ requests. Meanwhile, role changes between departments, like sales to finance, sit in limbo for days or even weeks.
Contractors finish short-term projects, but their JD Edwards access management credentials linger because no one has time to follow up systematically. Orphaned accounts stack up quietly in the background.
Financial and operational exposure in ERP systems
Now consider the real stakes for your bottom line. One employee retaining access to both vendor payments and invoice approvals in JD Edwards creates a segregation of duties violation just waiting to enable internal fraud.
A single unchecked permission set can lead to millions in undetected losses, as we've seen in high-profile cases across manufacturing and retail sectors. Operational disruptions compound the damage. Delayed access for new hires slows critical month-end financial closes by days.
Increasing compliance pressure (SOX, internal audits)
Regulators like SOX don't mess around anymore, especially with remote work and hybrid teams amplifying oversight needs. They demand hard evidence that every bit of JD Edwards access precisely matches the user's role, was approved by the right stakeholders, and was revoked promptly upon change or exit. With manual systems, the proof hides in fragmented sources.
Email chains from managers, ticketing systems overloaded with notes, and scattered spreadsheets that no one owns. Audit prep turns into a multi-week scramble. Teams spend days piecing it together, often missing key details under deadline pressure. Automated user provisioning flips the script.
Identity lifecycle gaps are a major attack surface
Industry reports peg the average time to fully remove access after employee termination is 27 days. That's a dangerously wide-open window for disgruntled insiders, lateral movement by external hackers, or simple credential-stuffing attacks.
In JD Edwards environments, where sensitive financial data and supply chain controls reside, these identity lifecycle gaps represent prime real estate for bad actors. Automated provisioning changes the scenario by linking directly to your HR systems like SAP SuccessFactors or Workday.
What Is Automated User Provisioning for JD Edwards?
Definition and core capabilities
At its core, automated user provisioning for JD Edwards leverages a robust IAM platform to orchestrate the entire user account lifecycle without requiring constant manual IT intervention.
Key capabilities cover automated account creation the instant HR processes a new hire, role-based access assignment tailored to their department and title, automated deprovisioning upon termination or contract end, and configurable approval workflows for edge cases like temporary escalations.
Think of a new hire record in Workday firing off provisioning in under five minutes, instead of relying on helpdesk tickets that pile up. This setup delivers proactive, always-on control.
How automated provisioning strengthens JD Edwards access management
Manual JD Edwards access management is riddled with persistent holes. Forgotten orphaned accounts remain active indefinitely, duplicate roles emerge from inconsistent admin practices, and permission updates languish in backlog queues. Automation imposes a single, reliable process at every lifecycle touchpoint.
Access exists only as long as business need dictates, backed by documented approval. Users receive precisely what's defined in their role profile. Over months of operation, this approach dramatically reduces standing privileges, uncovers hidden over-provisioning, and keeps your ERP environment cleaner, more defensible, and operationally efficient.
Automated Provisioning vs JD Edwards SSO: Understanding the Difference
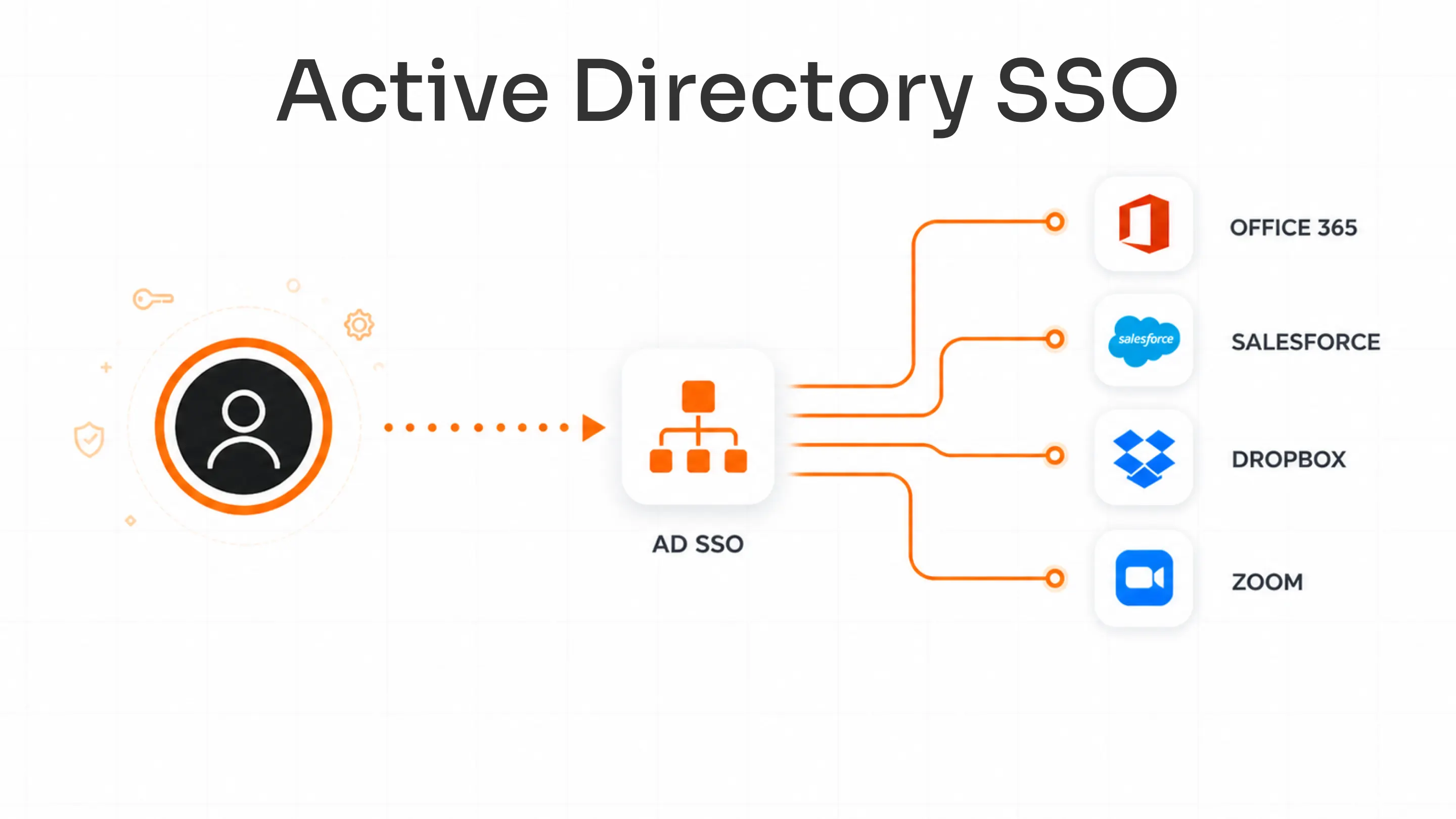
JD Edwards SSO centers on authentication. It verifies who you claim to be when attempting to log in, typically routing through a central identity provider like miniOrange, Okta, Azure AD, or Ping.
Automated provisioning takes charge of the authorization lifecycle. This includes determining what specific access rights you receive, dynamically updating them for role changes or promotions, and revoking them cleanly at tenure end.
| Dimension | JD Edwards SSO | Automated Provisioning |
|---|---|---|
| Primary function | Authentication (verifying identity) | Authorization lifecycle (managing access) |
| When it operates | At the point of login | Throughout the user lifecycle |
| What it controls | How users log in | What users can access and when |
| Trigger events | Login attempt | Hire, transfer, role change, termination |
| Governance impact | Centralizes login control | Enforces least-privilege and SoD policies |
| Audit contribution | Login events and session logs | Access history, approvals, certifications |
| Dependency | Requires an identity provider | Requires HR and IAM platform integration |
Platforms like miniOrange integrate JD Edwards SSO, MFA, and automated provisioning seamlessly. They manage everything through one unified policy engine.
5 Major Benefits of Automated User Provisioning for JD Edwards
1. Reduce Security Risks in JD Edwards Access Management
Security teams point to this as their top win. Automated user provisioning ensures JD Edwards access management grants permissions and revokes them precisely when business context demands. Terminated employees lose access immediately.
Least-privilege enforcement methodically takes away unnecessary extra access, curbing insider threats and blocking unauthorized peeks into high-risk finance or inventory modules. In terms of identity governance for ERP systems, it shrinks attack surfaces significantly. Industry best practices recommend keeping orphaned accounts nearly zero of total identities, as unmanaged accounts remain one of the most common entry points for unauthorized access.
2. Enforce Role-Based Access Control in JD Edwards
Role-based access control in JD Edwards truly excels under automation. The system maps every job function to predefined, tested access templates with zero variation.
Built-in segregation of duties (SoD) engines scan every request in real time, flagging high-risk conflicts such as procurement combined with approvals. Privilege creep, the steady accumulation of old roles over time, gets eliminated entirely. The end result is uniform enforcement that satisfies auditors and empowers operations teams with reliable, predictable access.
3. Improve Compliance and Audit Readiness for ERP Systems
Compliance officers see immediate value in the ERP user lifecycle management traceability. Every provisioning event logs immutably with full context: who requested, what changed, when it happened, and all approvals attached. Automated continuous access reviews surface outliers automatically on a quarterly cadence, prompting managers for quick sign-off.
Facing a SOX audit? Generate detailed reports on demand. Think complete access matrices, full change histories, and revocation proofs spanning years. Affected teams consistently report 70% faster preparation times, redirecting hours to proactive governance instead of fire drills.
4. Accelerate ERP User Lifecycle Management
The classic joiner-mover-leaver cycle transforms from bottleneck to seamless process. New joiners receive precise role-based access on day one via direct HR syncs. Movers get instant updates without dangerous permission overlaps.
Leavers trigger full revocation across endpoints in seconds. IT ticket volumes plummet significantly, manual errors disappear, and access governance standardizes reliably across global, multi-site teams. This consistency is what enterprise leaders seek for scalable operations, and they get it with the Joiner–Mover–Leaver process.
5. Integrate JD Edwards SSO, MFA, and Provisioning for Unified Security
Stack it with JD Edwards SSO for effortless logins and MFA for robust second-factor checks. Provisioning then gates what authorized users actually reach. Platforms like miniOrange deliver this as a unified IAM framework. Manage policies, monitor audits, and enforce rules from one console. Eliminate tool silos that breed gaps, and achieve airtight ERP security end-to-end.
Enterprise use cases of automated user provisioning for JD Edwards
Secure Employee Onboarding in JD Edwards
Consider a manufacturing firm handling 500 quarterly hires across plants. They used to endure 48-hour delays for basic access. Post-implementation, HR data entry triggers JD Edwards role-based access provisioning overnight. Finance teams hit the ground running on month-end closes without productivity dips.
Managing Role Changes Without SoD Violations
A sales representative transfers to finance. Automation instantly revokes sales dashboards, provisions ledger access, and executes SoD checks. No manual cleanup required, no surprises in the next audit.
Immediate Contractor Offboarding
With 2,000 contractors turning over yearly, end-of-contract dates now trigger instant JD Edwards revocation through vendor management system syncs. Lingering risks evaporate. No more tracking or juggling emails or forgotten accounts.
Audit Evidence Generation in Minutes
Quarterly SOX review due? Extract point-in-time reports on who held what access, complete approval paths, and deprovisioning confirmations. A task that consumed full weeks now resolves in 10 minutes per cycle.
How Automated User Provisioning Supports Identity Governance for ERP Systems
Provisioning goes beyond setup. It forms the heart of identity governance for ERP systems. Secure centralized visibility into all JD Edwards access. Direct complex requests through policy-driven approval workflows with escalations.
Conduct continuous access certification campaigns to eliminate drift quarterly. This maps directly to Zero Trust principles. Continuously verify roles against current needs and revoke access the instant context shifts. Adopting teams report measurably stronger audit pass rates and sharply reduced security incidents.
How IAM platforms enable automated user provisioning for JD Edwards
Required Capabilities
Reliable JD Edwards provisioning hinges on specific strengths. Native JD Edwards connectors enable deep API-level synchronization without brittle custom scripts. Workflow automation handles multi-step, multi-approver paths efficiently.
Role mining analyzes actual usage patterns to refine templates over time. SoD policy engines perform real-time conflict detection at request submission. Access review modules automate certification evidence generation. Avoid reinventing wheels. Prioritize platforms with mature, out-of-the-box integrations.
IAM platforms like miniOrange bundle these essentials. They offer provisioning, SSO, MFA, and governance purpose-built for ERP complexity, all accessible from a single dashboard for gap-free operations.
Transform JD Edwards access management with automated provisioning
Automated user provisioning for JD Edwards fortifies JD Edwards access management, optimizes ERP user lifecycle management, rigorously enforces role-based access control, and advances identity governance for ERP systems to enterprise-grade levels.
Evaluate your JD Edwards access lifecycle maturity and governance posture today. Pinpoint accumulating manual gaps, then deploy automation to eliminate them permanently and safeguard your operations.
Frequently Asked Questions
What is automated user provisioning for JD Edwards?
It is the use of an IAM platform to manage JD Edwards account creation, role assignment, access updates, and deprovisioning automatically through HR-triggered, policy-driven workflows, eliminating manual IT steps at every lifecycle event.
How does automated provisioning improve JD Edwards compliance?
It creates a structured, timestamped record of every access event, including approvals and deprovisioning confirmations, making SOX audit evidence available on demand instead of requiring manual reconstruction from scattered sources.
Can JD Edwards provisioning integrate with SSO and MFA?
Yes. Platforms such as miniOrange unify JD Edwards SSO, MFA, and automated provisioning in one IAM framework, providing centralized authentication, second-factor enforcement, and full access lifecycle governance.
What is the difference between SSO and automated provisioning for JD Edwards?
SSO governs how users authenticate at login. Automated provisioning governs what authenticated users can access and manages those permissions across their entire tenure. Both are necessary components of a complete identity governance program.
Which organizations benefit most from automated provisioning for JD Edwards?
Organizations with high user volumes, significant contractor populations, active SOX obligations, or frequent role changes see the clearest return. The value scales directly with lifecycle event volume and role complexity.

Leave a Comment