Why do access control challenges exist, despite most companies following it? The gaps could be due to inconsistent permissions, accumulation of accesses, or poor management of user lifecycles.
Access control is about governance. It answers two questions: “Who are you?” and “What are you allowed to do?” To add on, in today’s multi-cloud hybrid reality, governance is hard to handle.
This isn’t another theoretical deep dive. We’ll cut through the jargon to show you exactly where enterprises stumble, and what actually works to build resilient, audit-ready access management.
Access Control Challenges Keeping You Up at Night
Here’s a list of vulnerabilities that keep the security teams up all night:
1. Lack of Centralized View
In a fragmented architecture, the security teams deal with:
- Reconciliation of Active Directories (AD)
- Auditing Snowflake roles
- Chasing who approved a certain legacy mainframe access
These are just surface-level issues that security teams deal with in a distributed system. There’s no single source of truth for permissions. It is annoying and dangerous.
When you don’t know who has access to customer data, you cannot detect the misuse. And the auditors are likely to find gaps during ISO 27001 or SOC 2 checks.
The Solution: A centralized identity system or environment that normalizes permissions across cloud apps, directories, and databases. This gives you one view without ripping out the existing systems.
2. Privilege Creep: The Silent Threat
Privilege creep is nothing but the accumulation of permissions over a significant time period. These accesses are forgotten once a project or a job is done. Keeping these permissions active is a direct invitation to the threats. Only one breach, and the entire database is compromised.
For instance, an intern who needed temporary access to a database for a summer project still has it after 20 months. These forgotten permissions are later exploited by a malicious entity.
The Solution: If someone hasn’t used a permission in 60 days, auto-revoke it unless re-approved. Least privilege isn’t a one-time setup; it’s continuous hygiene.
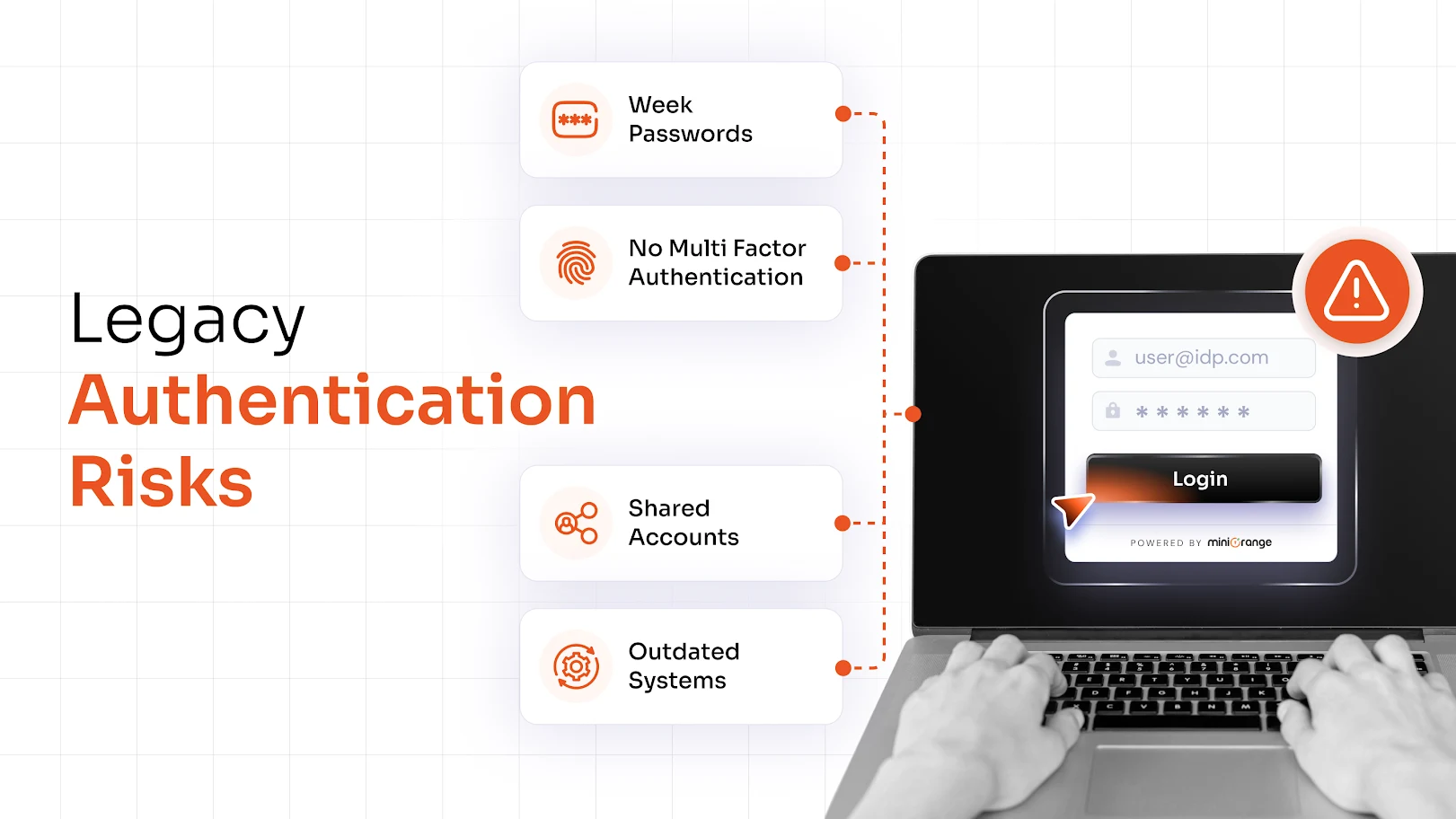
3. Shared Accounts: Accountability’s Worst Enemy
A shared account for the support team sounds efficient until there’s a need to trace who deleted sensitive data. Shared credentials affect audit trails, and sometimes usage of weak or reused passwords can lead to breaches.
The Solution: Replace passwords with JIT access, meaning grant temporary access to individuals with shared accounts/resources. You can pair this up with passwordless login options (FIDO2, grid pattern matching, or passkeys).
4. User Lifecycle: A Failure that Widens Security Gaps
A mismanaged onboarding may take three days or more. The same applies for offboarding: a Slack account may remain active because “someone forgot to deactivate the account.”
Furthermore, mismanagement can trigger role mismatches, too; for instance, a recently promoted manager may not be able to approve budgets.
The Solution: Make use of automated user lifecycle management to avoid the accumulation of dormant accounts and to speed up the onboarding process.
5. Hybrid Access Management: On-Prem, Cloud, and Beyond
Modern IT ecosystems blend on-premises servers, multi-cloud services, and third-party SaaS platforms. Controlling access consistently across all these environments is a major challenge. Different systems have different authentication and permission models, making unified enforcement difficult.
The Solution: Make use of federated identity management that integrates systems, ensuring consistent rules apply everywhere.
6. Broken Access Control Vulnerabilities
The Open Web Application Security Project (OWASP) puts broken access control at the number one position for web app risks. It is not like ransomware, but attackers somehow steal data, for example:
- A mobile app API that doesn’t re-check permissions on every request (letting users view others’ invoices by tweaking a URL).
- An admin panel accessible via a forgotten subdomain.
The Solution: Continuous testing, least privilege enforcement, and regular audits are key to preventing such breakdowns.
7. Problems with Monitoring and Reporting
Failed logins must be tracked, but that isn’t the only thing that enhances the effectiveness of monitoring. Detecting unusual access patterns, unauthorized activities, and privilege escalations amplifies monitoring and reporting. Organizations fail because their monitoring and reporting tools don’t integrate with their existing platforms, leaving blind spots.
The Solution: Automated reporting and monitoring, and adhering to tools that integrate with the pre-installed environments.
8. Policy Management Complexities
As businesses grow, their access policies multiply across applications, data types, user groups, and geographic regions. Keeping them consistent, updated, and auditable is a challenge. Even minor policy conflicts can trigger workflow issues or compliance risks.
The Solution: Centralized policy management frameworks enable teams to define, apply, and monitor policies from one location. Automation helps synchronize policy changes across environments in real-time, minimizing errors and administrative burden.
Overcome Access Control Challenges with miniOrange
miniOrange offers a unified, scalable platform that simplifies identity and access management for enterprises. Combining SSO solution, MFA solution, adaptive authentication, and robust user lifecycle management, it helps organizations close the gaps highlighted above.
Also, enterprises can eliminate privilege creep, enforce least privilege principles, and ensure compliance with evolving regulatory standards. miniOrange doesn’t just solve access control challenges; it sets the stage for future-ready identity management.
To know more about access control, get in touch with our security expert today!
FAQs
What elements does access control protect against?
Access control protects against internal misuse, unauthorized access, data breaches, and privilege escalation. It makes sure that only authorized users have access to systems.
What are the best practices of access control?
Best practices of access control include implementing Multi-Factor Authentication (MFA), enforcing the Principle of Least Privilege (PoLP), auditing permissions, centralizing visibility, and automating the user lifecycle process.
What are the 5 Ds of access control?
The 5 Ds of access control are Deter, Detect, Deny, Delay, and Defend. These represent the layers of digital and physical defense that holistically strengthen the security posture of an organization.
What are the 4 types of access controls?
The four standard types of access controls are RBAC, ABAC, DAC, and MAC. Each of these serves different organizational needs, depending on scale, flexibility, and confidentiality requirements.


Leave a Comment